Keeping files in a centralized database is by far the most common method of storing business data. This storage strategy has a downside, though. If you overlook database security, you create a treasure trove of valuable info that's both an easy and worthwhile target for cybercriminals.
This article outlines the most effective database security best practices for ensuring your files remain safe, confidential, and available.
What Is Database Security?
Database security is the practice of protecting files within a database from accidental and malicious threats. This subset of cybersecurity covers all the tools and measures teams use to:
- Prevent unauthorized access to files.
- Maintain data integrity.
- Ensure data stays available to users and apps.
Securing a database is difficult due to a wide attack surface. Most databases are network-accessible, so any threat within or in contact with the network is also a danger to the database. This wide surface means well-rounded database security must include measures for securing:
- Files within the database.
- The database management system (DMS).
- Applications and user accounts with access to the database.
- The database server (physical or virtual).
- The network infrastructure and communication channels used to access the database.
Database security naturally clashes with usability (the so-called Anderson's Rule). The more accessible a database is, the more vulnerable it becomes to security threats. Likewise, the better protected a database is, the more difficult it is to access and use stored files. One of the main goals of database admins is to find the right balance between usability and security.
Note: On the market for a new database server? PhoenixNAP's database servers enable you to host data on easy-to-deploy, workload-optimized hardware. We also provide 20 Gbps of DDoS protection free with every server to boost your database security.
Why Is Database Security Important?
Here's why maintaining high levels of database security is a priority for companies:
- Keep sensitive data safe. Database security protects valuable files (PII, customer records, financial data, business transactions, trade secrets, proprietary practices, etc.) from unauthorized modification or deletion.
- Maintain data availability. If someone takes down a database (willingly or accidentally), all systems that rely on the database stop operating. Such an event often disrupts business continuity and causes downtime, impacting your ability to generate revenue.
- Meet compliance obligations. Many industries have regulatory requirements for database security. Failure to comply with regulations results in penalties and legal consequences. The strictest regulations (such as SAO, PCI, HIPAA, or GDPR) come with fines that can exceed several million dollars per violation.
- Prevent data breaches. Database security reduces the risk of breaches and their consequences. A failure to maintain the confidentiality of data often leads to a loss of customer trust, high recovery costs, and legal problems.
Note: Learn about the three main threats to business data: breaches, leakage, and corruption.

Database Security Threats
Below are the most common and dangerous types of threats you must account for when creating a database security strategy.
SQL Injections
SQL injections are a type of cyberattack in which a threat actor inserts malicious code into a Structured Query Language (SQL) statement through an input field. If there's a vulnerability in the database code, the hacker bypasses the authentication and gains the ability to issue commands to the database.
SQL injections enable intruders to perform one (or several) of the following activities:
- Modify, steal, or delete data.
- Create new vulnerabilities to set up more advanced threats (e.g., an APT attack).
- Gain root access to the system.
- Compromise backend infrastructure.
While less common, there are also NoSQL injections. These attacks occur when an unsensitized query allows an intruder to include malicious input and execute an unwanted command on the NoSQL database.
Malware
Malware (short for malicious software) is an umbrella term for software-based threats (ransomware, spyware, adware, trojans, worms, viruses, etc.). Criminals introduce malware to databases in various ways, such as through:
- Infected software.
- An endpoint device connected to the database's network.
- Drive-by downloads.
- Trojans hidden within email attachments.
- Unauthorized on-site access to the database server.
Malware causes damage to the database in different ways. Malicious programs enable hackers to perform one (or several) of the following actions:
- Steal sensitive data.
- Destroy or modify files (e.g., a ransomware attack that encrypts all files within the database).
- Disrupt associated systems by crashing the database server.
- Create backdoors in the database.
- Gain remote access.
- Spy on data or keyboard inputs.
While most malware comes from outside your organization, remember that your strategy must also account for insider threats. An employee with malicious intent and authorized access to the database is a disaster waiting to happen.
Human Error
Here are a few mistakes that often jeopardize database security:
- Using and reusing weak passwords.
- Sharing passwords with other employees.
- Installing infected software on a BYOD device.
- Granting access to the wrong person (within or outside the organization).
- Sending messages with sensitive data to private social media or email accounts.
- Using shadow IT devices to transfer data from or to the database.
- Accidental erasure or corruption of data.
While there's typically no malicious intent behind these incidents, mistakes continue to be among the leading threats to database security. In 2022, uninformed user behavior was the cause of nearly half (49%) of all reported data breaches.
DMS Vulnerabilities
Criminals continually search for vulnerabilities in database management software (DMS). While companies behind both commercial and open-source database platforms release patches regularly, many users fail to install updates quickly enough to stop hackers from exploiting flaws.
There's also the danger of so-called zero-day attacks. These incidents occur when hackers discover an exploitable vulnerability in the DMS before the database vendor has a chance to patch the issue.
Password Attacks
Most databases use passwords as the main method of user authentication. Criminals often use bots to attempt to guess passwords, an approach that has several strategies:
- Brute-force attacks (systematically attempting to guess a password by trying different combinations of characters).
- Dictionary attacks (going through a list of commonly used words and phrases to attempt to guess the password).
- Password spraying attacks (using a list of commonly used credentials).
- Credential stuffing attacks (using a set of stolen usernames and passwords from other websites or databases to attempt to gain access).
Some criminals prefer stealing passwords instead of guessing them. Phishing, a form of social engineering, is the go-to technique for stealing credentials. Phishing attackers typically try to trick employees into typing in usernames and passwords in a fake login form.
Denial of Service (DoS) Attacks
A Denial of Service (DoS) occurs when an attacker overwhelms the database server with fake requests. The server then becomes unable to fulfill legitimate requests, causing the device to crash or become unstable.
DoS attacks typically have one of two goals:
- Halt business operations by causing resource exhaustion.
- Distract the security team while attackers perform other tasks (such as exfiltrating data or setting up malware).
A more challenging form of DoS is the distributed denial of service (DDoS) attack. In a DDoS, the fake traffic arrives from multiple servers (often malware-infected devices from unsuspecting users), making it significantly more difficult for the security team to stop the attack.
Note: Our article on DDoS prevention presents 7 tried-and-tested methods of stopping attackers from overwhelming a server with fake traffic.
Layers of Database Security
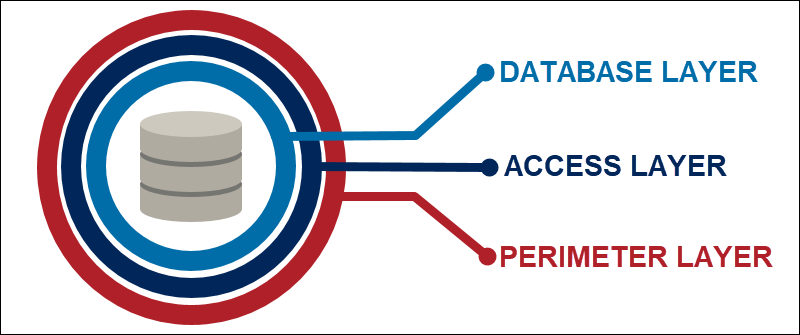
There are three primary layers of database security:
- Database layer.
- Access layer.
- Perimeter layer.
The table below offers explanations of all three security levels:
| Security layer | Description | Primary goal | Go-to techniques |
|---|---|---|---|
| Database layer | Protection of the data stored within the database | Ensure only authorized users access and modify stored files | Activity monitoring, tokenization, data masking, and encryption |
| Access layer | Protection of the mechanisms used to access the database | Ensure every access request is authenticated and authorized | Enforcing hard-to-guess passwords, 2FA, and permission controls |
| Perimeter layer | Protection of the network connected to the database | Monitor incoming traffic for signs of suspicious activity | Firewalls, VPNs, IDPSes, and network segmentation |
Database Security Best Practices
Protecting your database from threats requires a mix of different measures. Here's a total of 15 most effective database security best practices to protect your storage systems.
1. Ensure Physical Database Security
Whether the database server is in an on-site server room or a cloud provider's data center, the device must reside in a secure, climate-controlled environment.
If you rely on a third-party provider for hosting, you outsource all measures related to physical security. If you manage an on-prem data center, protect the database server with:
- Locks.
- Around-the-cloud video surveillance.
- Dedicated security personnel.
- Uninterruptible power supply (UPS).
- Fire protection systems.
- Proper cooling systems.
Log any physical access to the server and ensure only a select few have the authorization to configure the device.
2. Use 2FA and MFA
In 2022, over 67% of all data breaches included at least one set of compromised credentials. Instead of using risky single-factor authentication (SFA) methods that only require a password to log in, you should use:
- Two-factor authentication (2FA) for default users.
- Multi-factor authentication (MFA) for admin accounts.
Using MFA for all users is a popular option for your most sensitive databases. You should also boost database security by only allowing validated IP addresses to access files (one of several endpoint security measures that boost database protection).
Important: Using 2FA and MFA does not remove the need for hard-to-crack passwords. Learn how to create strong passwords that are easy to remember and impossible to guess.
3. Enforce the Principle of Least Privilege
The practical minimum number of users should have access to the database. The fewer people have access, the easier it becomes to protect files.
Apply the same principle to individual database elements and the actions employees can perform with files. Each account should only have access to the required tables and operations (for example, SELECT or INSERT). The same logic applies to nonhuman accounts, including:
- Daemons.
- Service accounts and principals.
- Application user accounts.
You should also rely on zero-trust security. This model validates identities and device compliance every time someone makes an access request.
4. Prevent SQL Injections
There are two main kinds of SQL injections:
- Classic SQLi (a hacker sending commands to the database and gathering results from the output).
- Blind SQLi (a hacker asking true or false questions and evaluating app responses to get answers).
Your team should stop both types of injections with the following measures:
- Parameterized queries.
- Input validation.
- Sanitization of user inputs.
- Web application firewalls (WAFs).
Note: Our article on SQL injections offers an in-depth look at how to identify and effectively prevent this type of cyberattack.
5. Use a Proxy Server
A proxy server checks requests before sending them to the database server. If someone sends bogues traffic or malicious requests (i.e., an SQL injection or a ransomware-infected executable), the proxy server contains the effects and isolates the threat.
While some companies use HTTP-based proxy servers, you should set up an HTTPS server to protect databases with sensitive info. An HTTPS server encrypts all data, giving the database an additional layer of security.
6. Maintain a Data Inventory (or Map)
Companies that store extreme amounts of data often do not know exactly where files reside and what protections keep them safe. To avoid such a scenario, maintain a detailed inventory that states the following:
- Where each data set resides (and in what state).
- What employees, accounts, and apps have access to files.
- What measures you use to protect individual data sets.
An inventory helps better manage your database security efforts, but also aids with:
- Risk management.
- Business impact analysis (BIA).
- Regulatory compliance.
- Patching prioritization.
Alternatively, create a data map to serve the same purpose as an inventory (or use both).
Also, conduct regular access reviews to ensure database permissions are flaw-free as teams grow and start new projects. These reviews enable security teams to delete old and unnecessary permissions.
7. Keep Database Servers and DMS Platforms Up to Date
Always use the latest version of your DMS. Apply patches (service packs, security hotfixes, cumulative updates, etc.) as soon as the vendor issues them to ensure criminals have no time to exploit vulnerabilities.
As an extra benefit, keeping your DMS up to date improves the stability of database performance.
Good patching hygiene also applies to all apps and systems with access to the database. A high level of database security won't help if an app with an outdated and vulnerable plugin has direct access to files.
8. Make Full Use of Encryption
Use encryption at rest to protect data from theft, cyber espionage, and leakage. Encryption makes files unreadable to both hackers and malicious insiders (i.e., anyone without a decryption key).
You should also use encryption in transit to protect files while they move between different systems. Ensure all connections to the database use TLS encryption.
Important: Learn about key management and best practices before you start encrypting business data.
9. Automatic Lockdown After Multiple Login Attempts
If a user mistypes a password multiple times, the database server must automatically lock that account from more login attempts. You can either:
- Lock accounts out for a pre-defined period of time.
- Instruct the user to contact the security team to regain access to the database.
Someone typing in the wrong password multiple times is a sign of password-based attacks. Limiting the number of attempts attackers have in that scenario is vital to keeping them out of the database.
10. Isolate Your Databases
Avoid keeping databases on the same server as applications (or even other databases). While it's easier and cheaper to keep everything on one server, that strategy creates various vulnerabilities that place data at risk.
As an extra precaution, use software-defined perimeters (SDP). This measure isolates the database to prevent it from appearing as a part of any particular user's network. That way, you make it difficult for intruders to locate and reach databases with lateral movement.
11. Run Penetration Tests
Hire ethical hackers to perform penetration tests against your database. Don't give the in-house team the heads-up about the test and instead see how both employees and the database stand up to a realistic attack simulation.
Performing occasional pen tests helps find vulnerabilities the team might overlook during pressure-free analysis. Such tests are vital to the security of all types of databases. Also, supplement discoveries from pen tests with regular vulnerability assessments.
12. Create Regular Data Backups
Perform regular data backups of all files in your databases. Follow the 3-2-1 backup rule:
- Create three copies of the data.
- Use two different types of storage.
- Store one copy in an off-site location (e.g., in the cloud).
If anything goes wrong with the files in your database (unwanted edits, accidental deletion, malware encrypting data, etc.), you restore information from the most recent backup and avoid data loss. Ensure the recovery process is quick and error-free with:
- Regular tests that ensure you're backing up data without corruption.
- A disaster recovery plan outlining the exact steps teams take if something happens to the data.
Note: As an extra precaution, use immutable backups, one of the most effective ways companies counter the threat of ransomware.
13. Use Real-Time Database Monitoring
All major database platforms come with built-in monitoring and logging capabilities. Use these tools to keep logs of:
- Who and when accesses the database.
- All data-related activities within the database (edits, deletions, adding new info, etc.).
- Failed login attempts.
- All devices connecting to the database.
- Info that provides additional context to database activity (e.g., network connections, authentication, Bytes In/Out, memory usage, etc.).
Remember that the quicker you react to database breaches, the more time you have to limit the blast radius. Use the following to speed up your reactions to threats:
- File Integrity Monitoring (FIM): FIM logs all actions carried out on the database server. When FIM detects a suspicious change, the platform sends an immediate alert to the security team.
- Security information and event monitoring (SIEM): Real-time SIEM helps security teams take immediate action in the event of an attempted database breach.
Set up behavior-based monitoring rules that help detect unusual user activity, such as making too many edits or logging in at suspicious hours.
14. Have Strict Controls and Policies
Establish strict company-wide policies that dictate the way teams use and manage the database. Define and document the following three rule sets:
- Admin controls that govern installation, change, and configuration management.
- Preventative controls that govern access, encryption, and masking rules.
- Detective controls that govern how the team monitors database activity and uses data loss prevention tools.
Integrate your database security policies with other cybersecurity policies (e.g., your cloud security policy).
Ensure everyone is aware of your policies by organizing regular awareness training programs. Such events are also an opportunity to educate staff members on the latest cybersecurity best practices and threats.
15. Use Firewalls to Monitor Database Traffic
Use firewalls to protect your database server from traffic-based threats. A firewall scans all incoming and outgoing traffic for signs of malicious packets, plus stops the database from starting unnecessary outbound connections.
Configure your firewall correctly to avoid security loopholes. Also, ensure the team keeps the firewall up to date with the latest patches to keep up with would-be hackers.
Most companies serious about security deploy more than one type of firewall. In most cases, these four are enough to keep your database safe from all network-based threats:
- Packet filter firewall.
- Stateful packet inspection.
- Proxy server firewall.
- Web application firewall (WAF).
Note: Learn about the different types of firewalls and see which ones make for the best fit with your database security needs.
Conclusion
Implementing the database security best practices discussed above is essential to protecting business data. Without these precautions, your company takes on too many unnecessary risks both to day-to-day operations and your bottom line.