SSH and SFTP are secure communication and file transfer mechanisms. However, they differ in purpose, function, transport mechanisms, and other factors.
The following text explores SFTP vs. SSH, do they differ, and how.
SFTP vs. SSH: Overview
When connecting to another machine remotely or transferring files between computers, it's essential to employ encryption. Encryption safeguards sensitive information like usernames and passwords. This security is established by using secure protocols like SFTP and SSH.
The following table represents the key differences between SFTP and SSH.
| SSH | SFTP | |
| Name | Secure Shell | Secure File Transfer Protocol. |
| Purpose | Provides authentication and secure logins. | Creates a secure channel for transferring files. |
| Security | Uses encryption to keep data in transit protected. | Uses SSH for encryption. |
| Authentication | Uses a public key or password. | Uses the same authentication methods as SSH. |
| Functionality | Used for secure remote communication and command execution. | Used for secure file transfer and manipulation. |
| File Transfer | Not designed for transferring files but provides a framework for it. | Provides secure file transfer over an SSH connection. |
| Port Usage | Port forwarding and tunneling on port 22 | Uses the same mechanisms as SSH. |
SFTP vs. SSH: In-Depth Comparison
SSH and SFTP share similar capabilities and are often used together, but they have distinct characteristics that set them apart. The following sections outline the primary differences between the two technologies.
Definition
While Secure Shell (SSH) and Secure File Transfer Protocol (SFTP) are network protocols, their definitions are not the same.
SSH is a network protocol that provides secure access to remote systems. SFTP, on the other hand, is a network protocol that operates over an SSH connection and enables secure file transfer between systems.
SSH ensures secure communication and authentication by encrypting data transmissions. SFTP, however, provides a safe and encrypted method for uploading, downloading, and managing files between computers.
Note: For more information on how these protocols work, check out our in-depth guides:
Function
Both SSH and SFTP have unique strengths which suit different use cases. While SSH provides secure command execution, SFTP focuses on secure file transfers.
SSH is an essential tool for network administrators and anyone requiring secure, remote access to a server. Apart from system administration, SSH is used for:
- Secure file transfer. With the help of protocols like SFTP, SSH transfers files between machines securely.
- Port forwarding (tunneling). SSH creates secure tunnels for other network services to enable secure operation over an insecure network.
- Command execution. SSH provides a secure shell on a remote server, allowing users to run commands securely.
Note: Find out how to use SSH to connect to a remote Linux or Windows server.
On the other hand, the primary function of SFTP is to protect file transfers across different operating systems. Its other use cases include:
- Secure file management. SFTP possesses robust file management capabilities, allowing users to handle files on a remote machine.
- Data backup and synchronization. SFTP is often used to back up and sync files remotely.
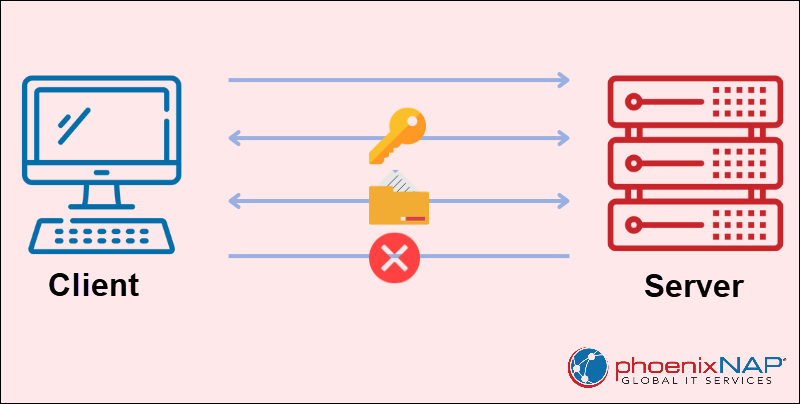
Authentication Method
SSH employs two main methods for authentication. The first is public key authentication, which is highly secure. The public key is shared with the remote server or client, and the private key is kept secret and must not be shared to prevent unauthorized access. The second method involves passwords, although it is less secure than public/private key authentication. In addition to authentication, SSH uses robust encryption algorithms to guarantee the confidentiality of data in transit.
Note: For more information, refer to our in-depth guide to Data in Transit Encryption.
SFTP relies on SSH for its authentication methods, using public key authentication as well. This means the same robust encryption and authentication mechanisms are in place, ensuring the secure execution of file transfers and management commands.
File Transfer Mechanism
SSH itself is not designed for transferring files. It is primarily a network protocol for securely connecting to remote servers and executing commands. However, it provides a secure framework for transferring files between the local and remote systems.
SFTP is one common method for securely transferring files over an SSH connection. When transferring files using the SFTP:
1. An SSH connection is established between the client and the server.
2. The client authenticates its identity to the server using a public key or other authentication methods.
3. An encrypted session starts, allowing the client to send and receive files to and from the server securely.
4. Once the data transfer completes, the client disconnects from the server and ends the session.
Note For more information, check out our comprehensive guide on how to use SFTP to transfer files.
Port Usage
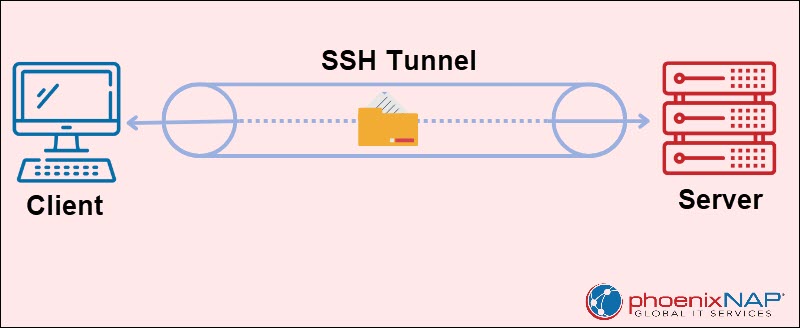
SSH port forwarding, or SSH tunneling, is a powerful tool for enhancing security and privacy. It encrypts data transmitted from one specific port to another, providing an effective way to protect network traffic and access resources securely. The default SSH port for SSH tunneling is port 22, the standard port for SSH communication.
There are two primary types of SSH port forwarding:
- Local. Forwards traffic from a local port on the machine to a remote server through an SSH connection. Local port forwarding enables access to services on a remote server, typically inaccessible from the local machine.
- Remote. Forwards traffic from a remote server to a local port on the machine through an SSH connection. Remote port forwarding allows remote systems to access services running on the local machine.
As this protocol is based on SSH, SFTP utilizes SSH tunneling to enhance security. This protects SFTP connections by routing them through SSH tunnels, ensuring file transfers remain secure.
SFTP vs. SSH: Frequently Asked Questions
SSH and SFTP share common characteristics. Therefore, it's not uncommon for users to not distinguish them. The following text answers some common questions regarding SSH and SMTP.
Are SFTP and SSH the Same?
No, SFTP and SSH are related but not the same. SFTP is a specialized protocol for secure file transfers that operates within the broader SSH framework. SSH is a more versatile protocol for secure remote access and management.
How Are SFTP and SSH Similar?
Both SFTP and SSH provide strong security by encrypting data and ensuring secure authentication. They support multiple methods for authenticating users, including public key and password authentication.
How Are SFTP and SSH Different?
SFTP and SSH, while sharing similarities, have distinct purposes and functions.
SFTP is specialized for secure file transfers, enabling the secure exchange of files between systems over a network. It focuses on file uploads, downloads, listing, and file management.
In contrast, SSH is a versatile protocol for securely accessing and managing remote systems. Beyond remote access, SSH offers a broader range of capabilities, including remote command execution, shell access, and secure network traffic routing through tunneling.
SFTP operates within an SSH connection, relying on SSH's secure communication framework. To use SFTP, establishing an SSH connection first is a must.
Conclusion
After reading this article, you know about SFTP vs. SSH differences and when to use them.
Next, learn about the differences between SSH and SSL.