The port number is a virtual concept in computer networking that provides a network identifier for a service or application. The number is a 16-bit integer from 0 to 65535 that, along with the IP address, creates a network communication socket.
This article shows how to open a port in Linux and use Linux networking tools to list and test open ports.
Prerequisites
- A Linux system.
- Administrative system access.
- Access to the terminal.
Listing Open Ports
Before opening a port on a system, check if the port you need is already open. The simplest way to do this is to pipe the output of the netstat command to the grep command.
netstat -na | grep :[port-number]The syntax above tells grep to look for a specific port number in the port list provided by netstat. For example, to check if port 8080 is available on the system, type:
netstat -na | grep :8080If the port is closed, the command returns no output.
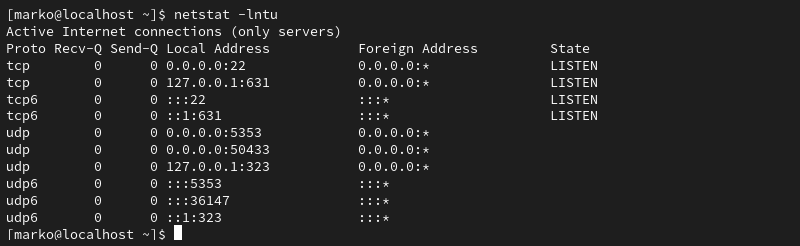
Alternatively, use the following netstat command to display a list of listening ports:
netstat -lntuThe -l option looks for the listening ports, -n provides numerical port values, while -t and -u stand for TCP and UDP, respectively.
Note: For more details on netstat syntax, read Netstat Command in Linux.
Opening a Port in Linux
The correct procedure for opening a port depends on the Linux distribution and the firewall you are using. The following sections provide steps for the three most common scenarios:
- The UFW firewall on Ubuntu-based distributions.
- firewalld on CentOS and other RHEL-based distributions.
- The iptables utility for the systems without UFW and Firewalld.
Note: Learn how to use GUFW, a GUI for UFW.
Ubuntu and UFW Based Systems
UFW (Uncomplicated Firewall) for Ubuntu allows you to open a port with a single command:
sudo ufw allow [port-number]The output confirms when you add IPv4 and IPv6 rules.

Alternatively, open the port used by a specific service without stating the port number:
sudo ufw allow [service-name]Note: After you finish creating the rules, ensure UFW is active on your system by typing:
sudo ufw enable
CentOS and Other Systems with firewalld
The firewalld tool on CentOS, Fedora, and other related distributions enables users to control port access on their system. The following command opens a specific port:
sudo firewall-cmd --zone=public --add-port=[port-number]/[protocol] --permanentThe --permanent option ensures that the rules persist after the system reboot.
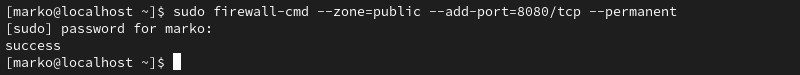
Note: The --zone=public argument is necessary only in multi-zone system configurations. By default, firewalld assigns all interfaces to the public zone.
Linux Distributions without UFW or firewalld
While installing a full-fledged firewall is the recommended way of maintaining system security, some Linux distributions still use the legacy iptables solution. The iptables utility allows configuring rules to filter IP packets using the Linux kernel firewall.
Use the following command to create an iptables rule for opening a port:
sudo iptables -A INPUT -p [protocol] --dport [port] -j ACCEPTThe command creates an IPv4 rule. To create an IPv6 rule, use the ip6tables command:
sudo ip6tables -A INPUT -p [protocol] --dport [port] -j ACCEPTThe port number is specified with the --dport option. The -p flag allows you to define the protocol (tcp or udp). For example, to create an IPv4 rule for the TCP port 8080, type:
sudo iptables -A INPUT -p tcp --dport 8080 -j ACCEPTMake iptables Rules Persist on Debian-Based Systems
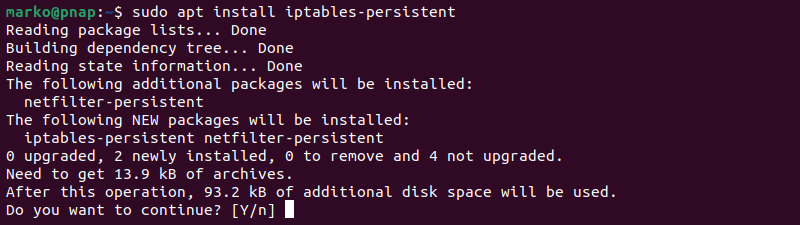
The rules created using iptables do not persist after reboots.
Follow the steps to restore iptables rules after a reboot on Debian-based systems:
1. Save the IPv4 rules you created:
iptables-save > /etc/iptables/rules.v42. Store any IPv6 rules in a separate file:
ip6tables-save > /etc/iptables/rules.v63. Install the iptables-persistent package:
sudo apt install iptables-persistentThis package automatically reloads the contents of the rules.v4 and rules.v6 files when the system restarts.
Make iptables Rules Persist on RHEL-Based Systems
RHEL-based systems store the iptables configuration in a different location.
1. Type the commands below to save the IPv4 and IPv6 rules, respectively:
iptables-save > /etc/sysconfig/iptablesip6tables-save > /etc/sysconfig/ip6tables2. Ensure the iptables-services package is installed:
sudo dnf install iptables-services3. Start the service:
sudo systemctl start iptables4. Enable the service:
sudo systemctl enable iptables5. Save the iptables rule:
sudo service iptables save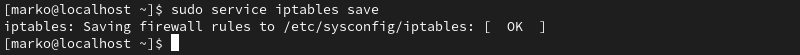
6. Restart the service to enforce the rule:
sudo systemctl restart iptablesTesting Open Ports
After using any of the methods above to open a port in Linux, ensure that the process is successful. The following methods are simple ways to check which ports are open on a system.
View the listening ports with the netstat command:
netstat -lntu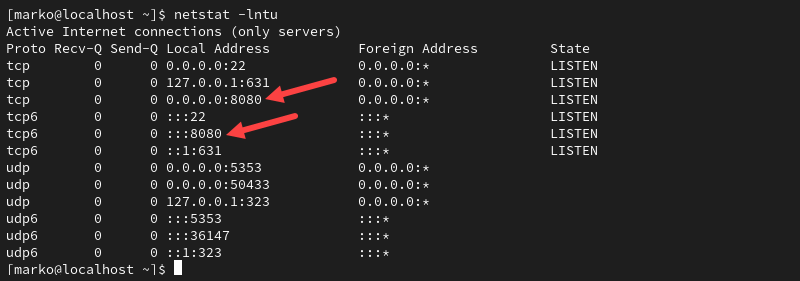
The output above shows the port 8080 we opened previously.
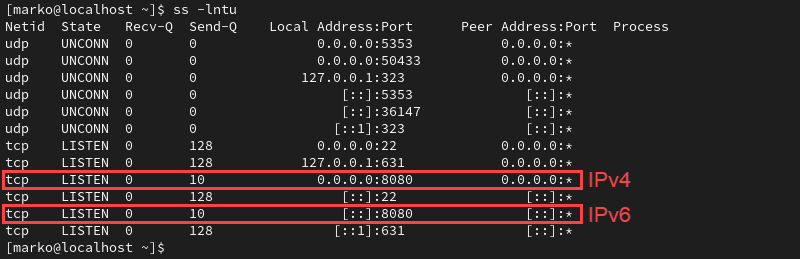
List the open sockets with the ss command:
ss -lntuThe port appears as part of the socket.
Note: To understand the function of sockets in Linux, refer to How Linux Uses Sockets.
Test the port by specifying its number to the nmap command.
nmap localhost -p 8080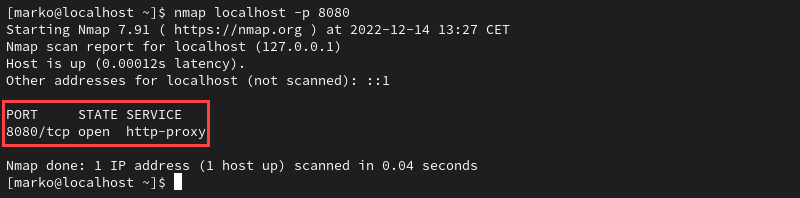
Test the Port with the Netcat Utility
The Netcat tool includes the nc command that you can use to test an open port. To do so:
1. Use a command such as echo to pipe output to Netcat and specify the port to listen to. The example below pipes a message to test port 8080:
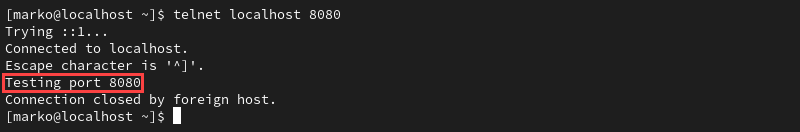
echo "Testing port 8080" | nc -l -p 80802. Leave the command running and open another terminal window.
3. In that terminal window, use a command such as telnet to query the local socket.
telnet localhost 8080If the port is open, the output of the telnet command contains the message piped to nc in step 1.
Note: Learn how to check for open ports in Linux.
Conclusion
This article provided instructions on opening and testing a port in Linux. Opening a port can be helpful for various reasons, such as allowing incoming traffic to access a specific service or application on your system.
Next, learn how to ping a specific port in Linux.