The ss (socket statistics) tool is a CLI command used to show network statistics. The ss command is a simpler and faster version of the now obsolete netstat command. Together with the ip command, ss is essential for gathering network information and troubleshooting network issues.
This article gives an overview of how to use the ss command and shows examples of the most common use cases.
Prerequisites
- Access to a terminal or command line
- Installed iproute2 software package
Note: Use the apt-get commands to install, update or upgrade the iproute2 software package.
Linux ss Command Examples
The basic ss command usage is without any parameters:
ssThe output returns a list of open non-listening sockets with established connections.
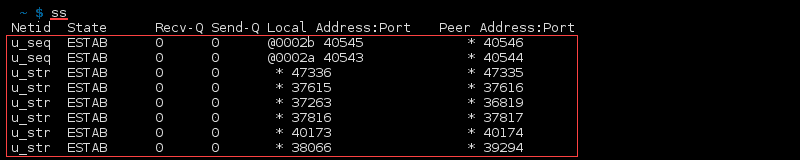
The columns show the following details:
- Netid – Type of socket. Common types are TCP, UDP, u_str (Unix stream), and u_seq (Unix sequence).
- State – State of the socket. Most commonly ESTAB (established), UNCONN (unconnected), LISTEN (listening).
- Recv-Q – Number of received packets in the queue.
- Send-Q – Number of sent packets in the queue.
- Local address:port – Address of local machine and port.
- Peer address:port – Address of remote machine and port.
For a more detailed output, add options to the ss command:
ss <options>Or list the options individually:
ss <option 1> <option 2> <option 3>Note: There are many Linux CLI tools for testing the network speed if the connection is slow.
List All Connections
List all listening and non-listening connections with:
ss -aOr:
ss --all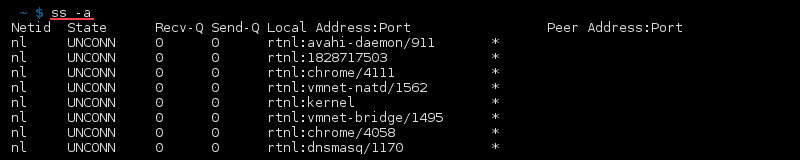
List Listening Sockets
To display only listening sockets, which are omitted by default, use:
ss -lOr:
ss --listen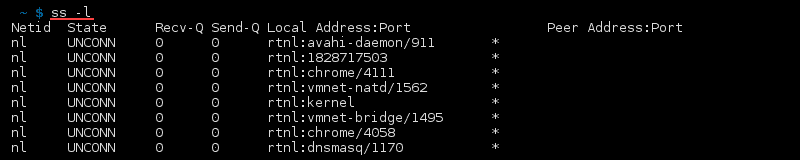
List TCP Connections
To list TCP connections, add the -t option to the ss command:
ss -tAlternatively:
ss --tcp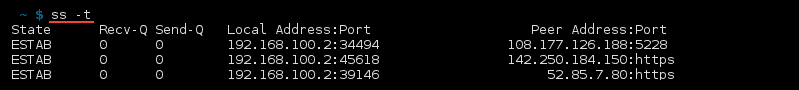
List All TCP Connections
Combine the options -a and -t with the ss command to output a list of all the TCP connections:
ss -at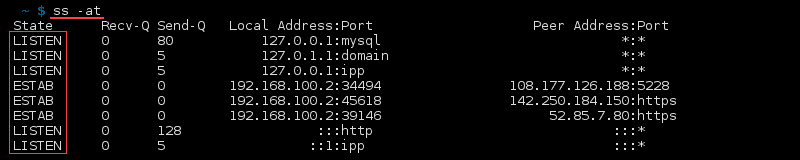
List All Listening TCP Connections
Combine the options -l and -t with the ss command to list all listening TCP connections:
ss -lt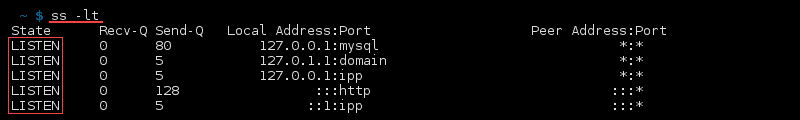
List UDP Connections
To show a list of UDP connections, use:
ss -uOr:
ss --udp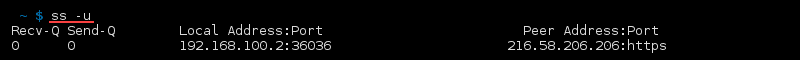
List All UDP Connections
Combining the options -a and -u with ss outputs a list of all the TCP connections:
ss -au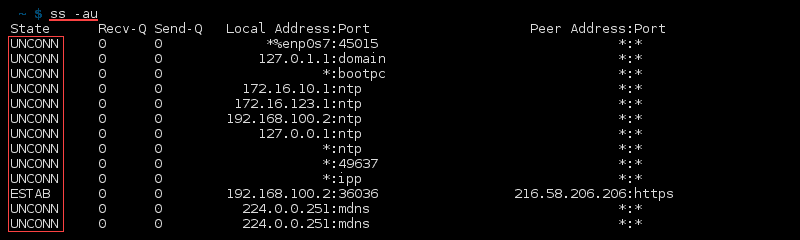
List All Listening UDP Connections
To list all listening UDP connections, use the ss command with options -l and -u:
ss -lu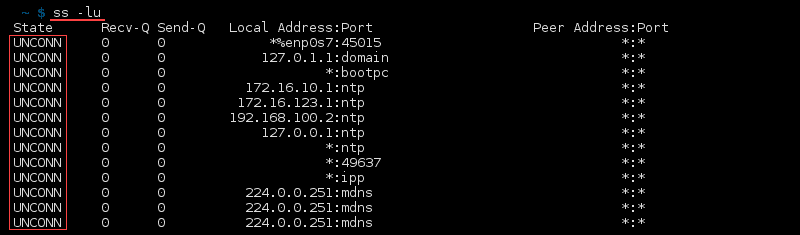
List Unix Sockets
To show all the Unix family sockets, use:
ss -f unixOr use the shorter alias:
ss -x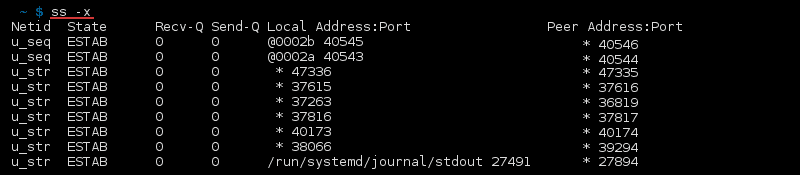
List Raw Sockets
To list raw sockets, use:
ss -wOr alternatively:
ss --rawList Connections to a Specific IP Address
List connections to a specific destination IP address with:
ss dst <address>For example:
ss dst 104.21.3.132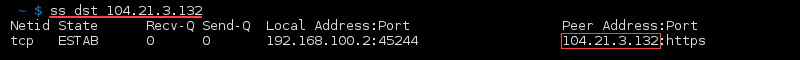
To show connections to a specific source address, use:
ss src <addresss>For example:
ss src 192.168.100.2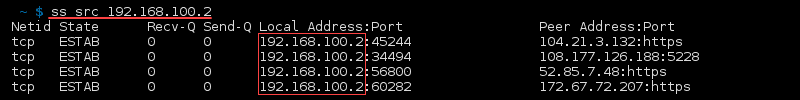
Note: To show all connections to the local machine, check your IP address and add the ss src command.
Check Process IDs
To show process IDs (PID), use:
ss -p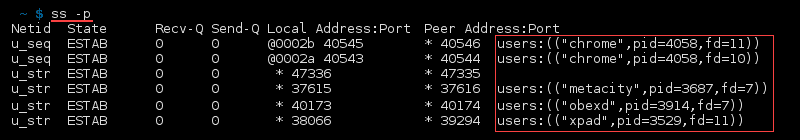
List Summary Statistics
List the summary statistics for connections with:
ss -s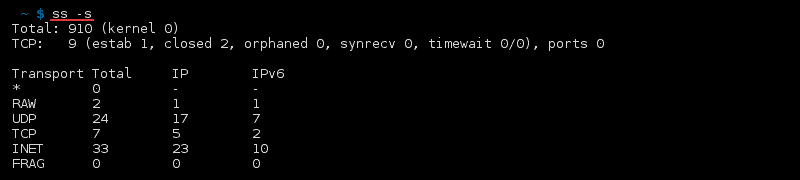
List IPv4 and IPv6 Socket Connections
Filter results further by listing IPv4/IPv6 connections with:
ss -4Or:
ss -6For example, list all IPv6 UDP connections with:
ss -au6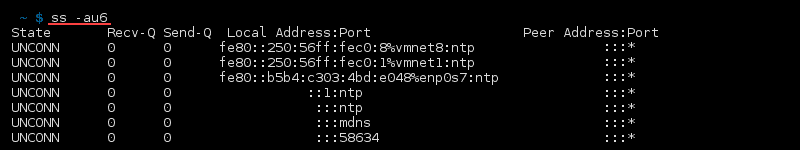
Filter Connections
The ss command allows advanced filtering of results and searching for specific ports or TCP states.
Filter Using TCP States
Filter TCP connections using the TCP predefined states:
ss state <name of state>For example, to find all listening TCP connections:
ss -t state listening
Filter by Port Number
Filter for a specific destination port number or port name:
ss <options> dst :<port number or name>For example:
ss dst :5228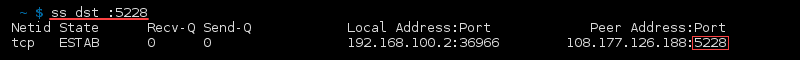
Or use a port name:
ss dst :https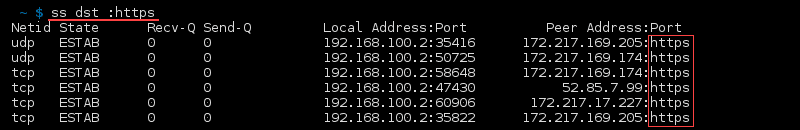
Combine multiple queries for more advanced filtering. For example, find all connections with a destination port 5228 or source port mysql:
ss -a dst :5228 or src :mysql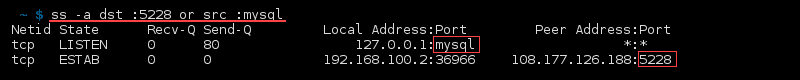
Check Man Pages or List All Commands
Check the manual page of ss in the terminal for a detailed overview of how to use the command:
man ssFor a quick overview of the available options, enter:
ss -hnetstat VS ss Command
The ss command is considered a replacement command for the obsolete netstat. The speed and better filtering options of CLI utilities from the iproute2 software package are preferable to the net-tools software package.
The netstat man page lists ss as the superior alternative. The netstat tool is still available to use. However, ss is a better and faster option.
Conclusion
The ss tool allows the investigation of socket and network statistics with advanced filtering options for a better troubleshooting experience. This utility is a must-know tool for any system and network administrator.
Check out our list of the best network security tools to minimize threats to your network environment.