What is a Mumble Server?
Mumble is an open-source voice over IP (VOIP) application widely used in the gaming community. Mumble consists of a server application (also known as Murmur) and a client application, which is installed for individual use.
Even though it can be used for any VOIP activity, it was primarily designed with gamers in mind so that they could communicate by connecting their clients to the same Mumble server.
Mumble Server Features
Murmur features a low latency service, a simple administration interface, and requires minimal server resources while supporting a wide range of high-quality audio codecs. Furthermore, Mumble and Murmur are BSD licensed and are completely free for commercial hosting.
End-users love it for its low latency, which makes it great for in-game use, as well as for its features, such as positional audio and in-game overlay.
Encryption
The control channel for delivering chat messages and non-time critical information is fully encrypted with TLS using 256-bit AES-SHA, while the voice channel is encrypted with 128-bit OCB-AES.
OS Support
Any platform that can compile Qt 4 supports Murmur. At the time of writing this article, this includes the most popular Linux distros, as well as Windows and MacOS X.
The Mumble end-user client is supported on most if not all popular operating systems, and there are even third-party apps for Android and iOS.
Prerequisites
- CentOS 7 server with at least 512MB of RAM
- bzip2
- Firewall port 64738 open for communication with Mumble clients
- SELinux disabled (if preventing Murmur from functioning properly)
Install Mumble Server
Download the Mumble Server Installation File
Mumble is not included in the official CentOS repository, so you will need to download the installation file from GitHub or the official Mumble server website.
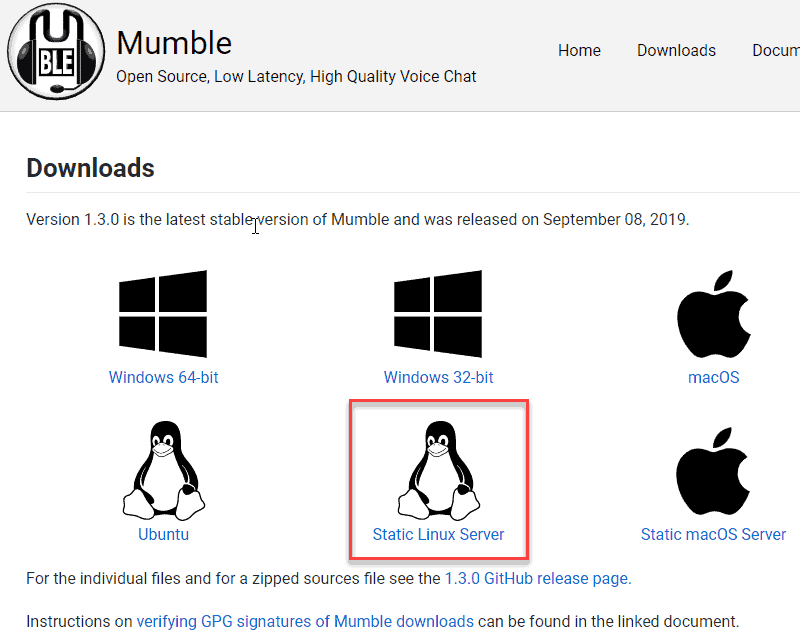
To download Mumble using a GUI, browse to the Mumble server website and select to download the install file for Static Linux Server.
To download Mumble using the terminal, use the wget command:
wget https://github.com/mumble-voip/mumble/releases/download/1.30/murmur-static_x86-1.3.0.tar.bz2 Extract Mumble Tarball
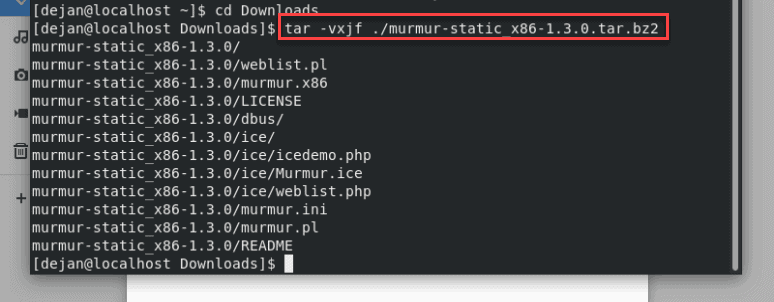
Now that you have downloaded the latest stable release of Murmur, you will need to extract the files from the tarball. First, you need to move into the Downloads folder. To do so, type:
cd DownloadsTo extract the file, run the following command:
tar -vxjf ./murmur-static_x86-1.3.0.tar.bz2Extracting the Murmur tarball should create a murmur-static_x86-[murmur version] directory.
If, on the other hand, you receive an error message as shown below, you will need to install the bzip2 package.
tar (child): bzip2: Cannot exec: No such file or directory
tar (child): Error is not recoverable: exiting now
tar: Child returned status 2
tar: Error is not recoverable: exiting nowTo install the bzip2 package, run the following command:
sudo yum install bzip2Once bzip2 is installed, re-run the command to extract the Murmur tarball. If prompted, type Y and press Enter to proceed.
Create a /usr/local/murmur Directory
This is where you will copy the extracted files from the tarball. To create the directory:
sudo mkdir /usr/local/murmursudo cp ./murmur-static_x86-1.2.19/* /usr/local/murmur/The next step will copy the configuration file to etc/murmur.ini.
sudo cp ./murmur-static_x86-1.2.19/murmur.ini /etc/murmur.iniNow, we’ll work on ownership and permission rules.
Create a Mumble Server User and Group, Logging and Data Directory
To create a User and Group, run the following commands:
sudo groupadd -r murmur
sudo useradd -r -g murmur -m -d /var/lib/murmur -s /sbin/nologin murmurTo create a Data and Logging directory, run the following commands:
sudo mkdir /var/log/murmur
sudo chown murmur:murmur /var/log/murmurFor the protection of logs, modify the permissions assigned to the log directory:
sudo chmod 0770 /var/log/murmurIt is highly recommended to rotate logs so that Murmur logs can’t fill up /var/log. As root, create a /etc/logrotate.d/murmur configuration file and copy-paste the following:
/var/log/murmur/*log {
su murmur murmur
dateext
rotate 4
missingok
notifempty
sharedscripts
delaycompress
postrotate
/bin/systemctl reload murmur.service > /dev/null 2>/dev/null || true
endscript
}Configure and Customize Mumble Server
All customizations are performed in the /etc/murmur.ini file. Before customizing anything, make sure the settings below are configured correctly in the /etc/murmur.ini file.
database=/var/lib/murmur/murmur.sqlite
logfile=/var/log/murmur/murmur.log
pidfile=/var/run/murmur/murmur.pid
# Reminder: When changing the port that murmur will listen to you will also need to update the firewall.
# Update the firewall by editing /etc/firewalld/services/murmur.xml
# Then run "sudo firewall-cmd --reload"
port=64738
# Comment out the following setting since the service will already be executing as the correct user:
# uname=murmurTo change the welcome message, modify the text following the welcome text string. Basic HTML markup is supported.
To change the user limit, find and modify the users=100 string. For example, if you want to reduce the number of slots to 50, the string should read users=50. If you want to limit per-user incoming bandwidth, find and modify the bandwidth parameter.
For added security, uncomment the autoban lines.
Create a Mumble Service
Create a system unit file in order to manage the Mumble server with systemd. Create a /etc/systemd/system/murmur.service file under root access or with sudo. Once created, copy and paste the following into the file:
[Unit]
Description=Mumble Server (Murmur)
Requires=network-online.target
After=network-online.target mariadb.service time-sync.target
[Service]
User=murmur
Type=forking
ExecStart=/usr/local/murmur/murmur.x86 -ini /etc/murmur.ini
PIDFile=/var/run/murmur/murmur.pid
ExecReload=/bin/kill -s HUP $MAINPID
[Install]
WantedBy=multi-user.targetModern systems discard /var/run after reboot. Create a /etc/tmpfiles.d/murmur.conf configuration file to restart the pid directory for Murmur. As root, copy-paste the following:
d /var/run/murmur 775 murmur murmurFirewall Rules
By default, a server’s firewall does not allow the service to listen to TCP/UDP. Modify the instructions below accordingly if you have customized murmur.ini to listen to a non-default port.
MurmurMumble Server (Murmur)<!– Reminder: Update /etc/murmur.ini so that it uses the same ports –>Add the firewall rule and then reload:
sudo firewall-cmd --permanent --add-service=murmur
sudo firewall-cmd –reloadDisable SELinux
Some versions of CentOS will have issues running Murmur without disabling SELinux. According to Mumble, SELinux will not prevent Murmur from functioning as of CentOS 7.2.
Initially, run the Mumble server with SELinux in enforcing mode. If SELinux is preventing Mumble from working correctly, the easiest solution is to disable it. To temporarily disable SELinux, run the following command:
sudo setenforce 0SELinux will restart upon reboot.
To permanently disable SELinux, edit the /etc/sysconfig/selinux file and modify the SELINUX line. It should read the following:
SELINUX=disabledReboot the server after disabling SELinux.
Start the Mumble Server
The following command will temporarily start the Mumble server and keep it running until the next reboot:
sudo systemctl start murmur.serviceTo stop the Mumble Server service, run the following command:
sudo systemctl stop murmur.serviceTo instruct CentOS to automatically start the service upon next reboot, run the following command:
sudo systemctl enable murmur.serviceIf you notice a “zombie process” when starting Murmur, you must install the redhat-lsb-core package.
Note: A zombie process is a leftover process that has not entirely ended. Programs designed for Linux are not meant to do that. Even though zombie processes take the slightest amount of resources, Linux distributions have a finite number of process IDs, so it is advisable to resolve this issue.
Conclusion
By following the steps outlined above, you have learned how to set up a mumble server and how to install Murmur on CentOS 7. Your users can use the domain name or IP address of the server and the default port (64738) to connect to the server.