Data is now one of the most valuable assets for businesses of all kinds, supporting everything from daily operations and communication to transactions and AI model training.
Yet, this value also makes data a prime target for cybercriminals and other malicious actors who seek to steal sensitive information to sell on the dark web or leverage it for ransomware attacks. Without the right security measures, your data is also at risk of accidental disclosure, alteration, or even destruction. Securing this data protects your company’s assets and ensures compliance with increasingly strict data protection laws.
This article will guide you through the essentials of business data security, covering core components, best practices, must-have tools, and the dire consequences that can result from neglecting data protection.

What Is Business Data Security?
Business data security refers to the collective measures and protocols organizations implement to protect their data from cyber attacks, unauthorized access, and data breaches. It includes a broad spectrum of practices aimed at ensuring the confidentiality, integrity, and availability of data:
- Confidentiality means that sensitive information is accessible only to authorized individuals.
- Integrity involves measures that guarantee data remains accurate and unaltered during its lifecycle.
- Availability ensures that data is accessible to authorized users whenever needed.
Data security is not just a concern for the IT department.
It is a fundamental aspect of corporate governance, as it involves coordination across various departments, including IT, legal, human resources, and executive management.
What Are the Elements of Business Data Security?
Effective data security builds upon the following elements.
Access Control
Access control mechanisms are fundamental to data security, ensuring only authorized personnel can access specific data and systems. Here are the core components of access control in data security:
- Authentication. Verifying the identity of users through credentials such as passwords, biometric scans, or security tokens.
- Authorization. Determining user privileges and permissions based on their role within the organization.
- Multi-factor authentication (MFA). Adding layers of security by requiring two or more verification methods before granting access.
- Single sign-on (SSO). Allowing users to access multiple applications with one set of login credentials, improving security and user convenience.
Encryption
Encryption protects data by converting it into a coded format that is unreadable without the appropriate decryption key. Here are the main types of encryption for protecting data:
- Data-at-rest encryption. Securing stored data on devices, databases, and backup media using encryption algorithms like AES-256.
- Data-in-transit encryption. Protecting data transmitted over networks using protocols like TLS/SSL for secure web communications.
- End-to-end encryption. Ensuring that data remains encrypted from the sender to the recipient.
Read our article on encryption key management best practices.
Network Security
Network security involves protecting the usability and integrity of network infrastructure. Here are the essential elements of network security:
- Firewalls. Acting as a barrier between trusted and untrusted networks, controlling incoming and outgoing traffic based on predetermined security rules.
- Intrusion detection systems (IDS). Monitoring network traffic for suspicious activities and taking action to prevent attacks.
- Virtual private networks (VPNs). Creating secure, encrypted connections over public networks for remote access.
- Network segmentation. Dividing the network into smaller segments to limit the spread of attacks.
Security Policies and Procedures
Formalized policies and procedures provide a framework for consistent and effective data security practices. Here are the foundational policies and procedures for data security:
- Acceptable use policies. Defining permissible activities for users when accessing company resources.
- Incident response plans. Outlining the steps to take in the event of a security incident, including roles, communication protocols, and recovery procedures.
- Compliance standards. Ensuring adherence to regulations such as GDPR, HIPAA, or PCI DSS, which mandate specific data protection measures.
- Data classification policies. Categorizing data based on sensitivity and applying appropriate security controls.
Employee Training and Awareness
Human error is a factor in 68% of data breaches. Educating employees reduces the risk of inadvertent security lapses. Here are the critical components of effective employee training in data security:
- Regular training sessions. Providing up-to-date information on security threats, such as phishing, social engineering, and malware.
- Phishing simulations. Testing employee vigilance through simulated phishing attacks to reinforce training.
- Security awareness training. Promoting a security culture through communication, reminders, and recognition of good practices.
Physical Security
Protecting physical assets is essential to prevent unauthorized access to hardware and facilities. Here are the primary measures for ensuring physical security:
- Secure facilities. Implementing access controls, such as key cards, biometric scanners, and security personnel at data centers and offices.
- Hardware security. Using locking mechanisms for servers, laptops, and storage devices to prevent theft or tampering.
- Environmental controls. Maintaining optimal conditions (temperature, humidity) and installing fire suppression systems to protect hardware from environmental hazards.
- Surveillance systems. Deploying cameras and monitoring equipment to deter and detect unauthorized physical access.
Data Backup and Recovery
A backup strategy ensures you can restore data in the event of loss due to hardware failure, cyber attacks, or disasters. Here are the essential practices for data backup and recovery:
- Regular backups. Scheduling automated backups to secure data repositories.
- Redundant systems. Implementing failover mechanisms to maintain availability.
- Offsite storage. Keeping backups in geographically separate locations to mitigate localized risks.
- Testing recovery procedures. Regularly verifying that backups can be restored successfully.

Types of Business Data Security
Various aspects of business operations require security measures tailored to their unique vulnerabilities.
Application Security
Application security focuses on protecting software applications from external threats and internal vulnerabilities. To protect software applications, focus on:
- Secure coding practices. Writing code free from common vulnerabilities like SQL injection, cross-site scripting (XSS), and buffer overflows.
- Code reviews and testing. Conducting static and dynamic analysis to identify and remediate security flaws before deployment.
- Application firewalls. Using web application firewalls (WAFs) to filter and monitor HTTP traffic to and from web applications.
- Regular updates and patching. Ensuring that applications are up-to-date with the latest security patches.
Cloud Security
As businesses increasingly rely on cloud services, securing cloud environments becomes imperative. To secure cloud environments, consider:
- Secure cloud configurations. Following best practices for setting up cloud services, including identity and access management, encryption, and network security groups.
- Cloud access security brokers (CASBs). Providing visibility and control over data movement between on-premises systems and cloud environments.
- Vendor management. Assessing cloud providers' security measures and compliance certifications (ISO 27001, SOC 2).
- Shared responsibility model. Understanding the division of security responsibilities between the cloud provider and the customer.
Check out our in-depth article on cloud security to learn how to protect sensitive data and applications stored in the cloud.
Mobile Security
With the proliferation of smartphones in the workplace, mobile device security has become vital. To protect mobile devices, implement:
- Mobile device management (MDM). Centralizing the management of mobile devices to enforce security policies, update software, and manage applications.
- Encryption of mobile data. Protecting data stored on mobile devices using device-level or application-level encryption.
- Secure mobile applications. Developing or deploying mobile apps that adhere to cybersecurity best practices.
- Bring-your-own-device (BYOD) policies. Establishing guidelines for personal device usage in the workplace to mitigate risks.
Endpoint Security
Endpoints such as laptops, desktops, and IoT devices are common targets for attackers. To protect endpoints, employ:
- Antivirus and anti-malware software. Detecting and preventing malicious software from compromising endpoints.
- Endpoint detection and response (EDR) software. Providing real-time monitoring and detection of endpoint threats.
- Device hardening. Configuring devices to minimize vulnerabilities by disabling unnecessary services and ports.
- Regular updates. Ensuring that operating systems and applications on endpoints are using the latest patches.
Every endpoint is a potential entry point for hackers.
Read our article on endpoint security to ensure these devices do not become a doorway to your assets and data.
Data Backup and Recovery
To ensure data availability, an effective backup and recovery strategy is essential. This strategy has three components:
- Disaster recovery planning. Developing comprehensive plans that outline recovery strategies for various scenarios, including natural disasters, cyber attacks, and system failures.
- Business continuity planning. Ensuring that critical business functions can continue during and after a disaster.
- Recovery time objectives (RTO) and recovery point objectives (RPO). Defining acceptable downtime and data loss thresholds to guide recovery efforts.
Which Businesses are Most Exposed to Risks?
The following industries face higher exposure to data security risks due to the sensitive nature of their data.
- Financial services. Oversee sensitive financial and personal data, making them prime targets for fraud and identity theft. Strict regulations like the Gramm-Leach-Bliley Act (GLBA) and Payment Card Industry Data Security Standard (PCI DSS) govern their operations.
- Healthcare organizations. Store protected health information (PHI), which is highly sensitive and valuable on the black market. Regulations like HIPAA impose stringent security requirements.
- Ecommerce platforms. Process large volumes of payment card information and personal data, attracting cybercriminals seeking financial gain.
- Technology firms. Possess valuable intellectual property and user data, making them targets for corporate espionage and data theft.
- Government agencies. Manage classified and sensitive information critical to national security. They frequently face threats from nation-state actors.
- Educational institutions. Maintain extensive personal records and research data, often with limited security budgets and resources.
- Energy and utilities. Operate critical infrastructure that, if compromised, has a widespread societal impact.
- Manufacturing companies. Increasing use of industrial IoT devices introduces vulnerabilities that can be exploited to disrupt operations.

How to Secure Business Data?
Here are eighteen strategies to enhance your organization's data security:
1. Develop a Comprehensive Security Policy
Establish a detailed IT security policy outlining your organization's data protection objectives. This policy must define roles and responsibilities, set protocols for data handling, and be regularly updated to reflect technological advancements and regulatory changes.
Involving stakeholders from various departments ensures the policy is practical and aligned with business goals.
2. Implement Strong Access Controls
Limit data access to authorized personnel only. Use role-based access control to assign permissions based on job functions, adhering to the principle of least privilege. To prevent unauthorized access and insider threats, regularly review and update access rights, especially when employees change roles or leave the company.
3. Use Encryption Effectively
Use robust encryption methods to protect sensitive data. Even if hackers intercept or access your data, encryption ensures it remains unreadable. Proper encryption key management is crucial for maintaining data security and meeting compliance requirements.
4. Keep Systems and Software Updated
Regularly update and patch all software and systems to guard against known vulnerabilities. Automated update processes reduce the risk of human error and ensure the timely deployment of critical patches. Also, you must not overlook updates for third-party applications and plugins.
5. Conduct Regular Security Assessments
Perform regular security audits and vulnerability assessments to identify weaknesses. Penetration testing simulates cyber attacks to uncover hidden vulnerabilities, allowing you to address them proactively. Use these insights to strengthen your security measures and policies.
Read our article on vulnerability scanning vs. penetration testing to learn about the differences between these two methods.
6. Train Employees
Educate your staff on recognizing phishing attempts and avoiding social engineering traps. Regular training sessions promote a culture of security awareness and reduce the risk of human error. You must also encourage open communication about security concerns and provide clear guidelines for reporting suspicious activities.
7. Use Advanced Security Tools
Deploy firewalls, antivirus software, and intrusion detection systems to protect your network and devices. Ensure these tools are updated to defend against the latest threats. Advanced security tools help detect and block malicious activities before they can cause harm.
8. Implement Data Loss Prevention Measures
Adopt data loss prevention (DLP) solutions to monitor and control the movement of sensitive data within your organization. DLP tools help prevent unauthorized access and transmission of critical information by enforcing data handling policies and setting up alerts for potential breaches.
9. Secure Mobile Devices
Implement policies and technologies to secure mobile devices used within your organization. Consider enforcing encryption, using mobile device management solutions, and establishing clear BYOD policies to mitigate risks associated with personal devices accessing company data.
10. Regularly Back Up Data
Maintain regular backups of critical data to ensure you can recover information in the event of loss due to hardware failure, cyber attacks, or other disasters. Store backups securely, preferably offsite or in the cloud, and test recovery procedures to ensure data can be restored quickly when needed.
11. Monitor Network Activity
Implement real-time monitoring of network traffic and system activities to quickly detect and respond to security incidents. Tools like security information and event management (SIEM) systems aggregate and analyze logs from various sources, enabling proactive threat management.
12. Establish an Incident Response Plan
Develop a clear plan for responding to security incidents, outlining procedures for identification, containment, eradication, and recovery. Assign specific roles and responsibilities to team members and establish communication protocols for internal and external stakeholders. Regularly test and update this plan to ensure its effectiveness.
13. Manage Third-Party Risks
Assess the security practices of vendors and partners with access to your data or systems. Limit their access to only what is necessary for their functions and include security requirements in contracts and agreements.
Software supply chain attacks are set to cost businesses a staggering $138 billion annually by 2031, a 15% increase year-over-year.
14. Secure Cloud Services
Ensure that cloud services used by your organization are configured securely and choose reputable cloud providers that comply with industry security standards. You must also understand the shared responsibility model of cloud security and implement the necessary measures to protect your data in the cloud.
15. Implement Physical Security Controls
Protect physical assets by controlling access to facilities and hardware. Use key cards, biometric scanners, and surveillance cameras to deter and detect unauthorized access. Additionally, you must develop procedures for securely disposing of or recycling sensitive data hardware to prevent information retrieval from discarded devices.
16. Enforce Strong Password Policies
Implement policies requiring strong passwords and regular password changes. Encourage the use of password managers to help employees manage complex passwords securely. Implement multi-factor authentication to add a layer of protection beyond passwords.
17. Ensure Regulatory Compliance
Stay informed about relevant data protection laws and industry regulations applicable to your business. Develop compliance programs and train employees on their obligations. Additionally, consider conducting external audits to verify compliance and address any gaps.
18. Use Network Segmentation
Divide your network into segments based on function or sensitivity to restrict the spread of potential attacks, including lateral movement. Apply strict access controls and monitor traffic between segments for unusual activity. Network segmentation enhances security by isolating critical systems from general network traffic.
phoenixNAP’s Data Security Cloud provides advanced security and compliance features tailored to meet regulatory requirements.
We use region-specific data centers and robust encryption methods to ensure your data is stored and processed in compliance with relevant laws. We also have comprehensive logging, auditing mechanisms, and IAM policies to maintain strict access controls and facilitate easy compliance audits.
Why Is Data Security a Priority for Businesses?
Here is why securing your business data should be a top priority:
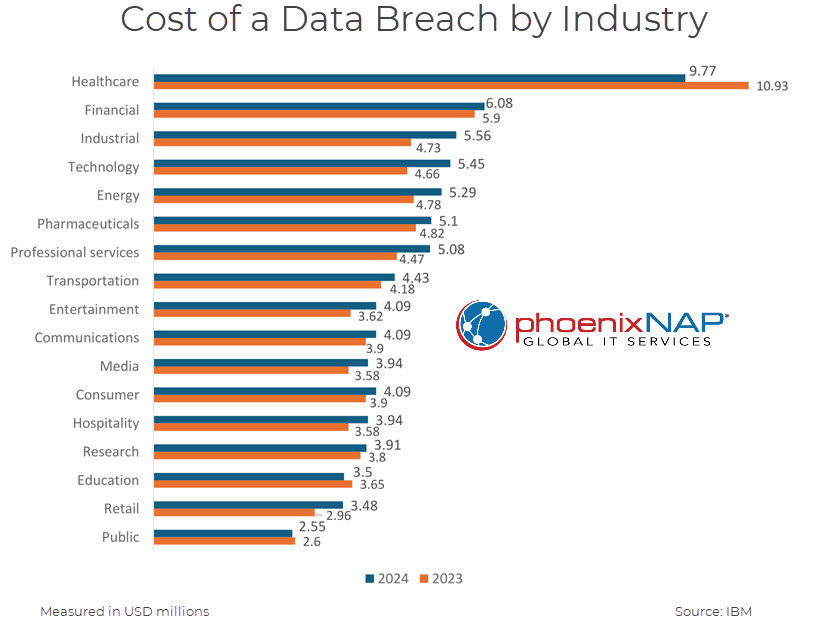
- Prevent financial losses. An average data breach in 2024 costs $4.8 million. This figure includes expenses for system repairs, cybersecurity consultations, and customer notifications. Cybercriminals may also encrypt your data and demand a ransom, causing immediate financial loss and potential operational downtime.
- Avoid penalties and fines. Laws like GDPR, HIPAA, and CCPA require strict data protection measures. Non-compliance leads to hefty fines and legal actions. Customers and partners affected by data breaches may also file lawsuits, leading to additional costs.
- Protect competitive edge. Protecting trade secrets, product designs, and business strategies prevents competitors from gaining an unfair advantage.
- Ensure business continuity. Robust data security minimizes the risk of disruptions caused by cyber attacks or data loss. Additionally, backup solutions enable quick recovery, reducing downtime.
- Reduce insurance costs. Demonstrating strong cybersecurity leads to reduced premiums for cyber insurance policies.
- Protect supply chain integrity. Robust data security practices reassure your organization’s suppliers and partners, maintaining your reputation.
Data Security: The Cornerstone of Business Success
Neglecting data security has serious consequences, potentially threatening a company's very existence. Protecting sensitive information shows an organization's commitment to reliability and trustworthiness to customers, stakeholders, and partners. This commitment nurtures loyalty and provides a significant advantage. In a data-driven world, investing in security is a strategic imperative that protects your business and positions it for long-term success.