As you read this article, your browser connects to the Internet Service Provider (ISP). The packets sent from your computer found their way to the server that hosts this website. The BGP (Border Gateway Protocol) decides which paths to take along the way.
If a router is not working or has high traffic load, the packets take another route. BGP accepts advertised routes from other BGP routers by default. There is no announcement of the path or the owner, leaving a significant security issue.
This article explains the RPKI protocol as a solution for secure BGP routing.
What is BGP?
The BGP protocol is the main protocol facilitating routing exchange through the Internet. Packets travel globally in a decentralized manner with automated routing. As data passes from one router to another, the information moves closer to the desired destination.
Each router maintains a locally significant best path table for each IP address prefix destination group. An AS (Autonomous System) owns groups of prefixes and determines how routing exchange happens. Each AS has a unique identifier (Number) and the BGP protocol defines how autonomous systems exchange information about IP routing.
Each ASN advertises prefixes to which it can deliver data. For example, if an AS connects to 1.0.0.0/8, it will broadcast the address to peers and providers.
Shortcomings of BGP
BGP route acceptance depends on the ISP engineering. The ISP due diligence only goes so far: input errors, automation blunders and malicious intent are just some examples which are hard to mitigate against. Ultimately, the core of the problem is there is no ground truth as to who should announce the path or who the real owner is.
Information sent through the Internet has limited protection against BGP Hijacks. A BGP hijack happens when an AS makes a BGP announcement for equal or more specific IP prefixes which the AS does not own.
Equal Prefix Length Hijacks
An equal prefix length hijack happens when someone who is not the owner announces the same prefix. For example:
- Origin AS sends data destined for 1.0.0.0/8
- Destination AS announces 1.0.0.0/8.
- A different AS also announces 1.0.0.0/8.
When an equal length announcement happens, the BGP must select a route. The decision comes down to the AS configuration.
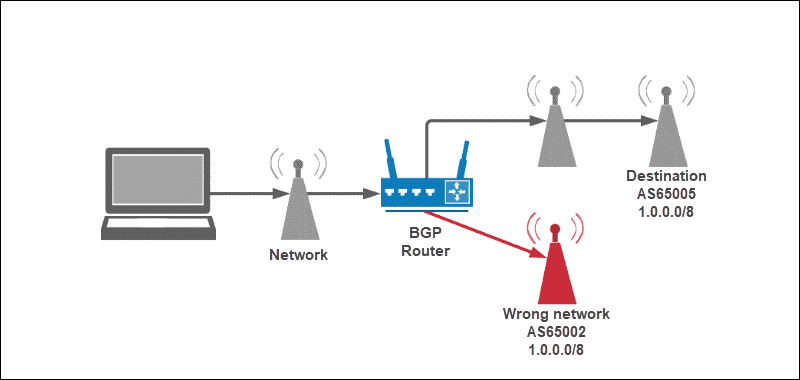
The origin AS notices a slight drop in traffic. The drop in traffic is a common occurrence which could happen for any number of reasons. Due to this, the BGP hijack goes unnoticed.
Specific Prefix Hijack
Specific prefix hijacks happen when a malicious ASN announces a more specific prefix. Both prefixes are added to BGP routing table, but the more specific address is selected as the best path to a network.
For example:
- Origin sends data destined for 1.0.0.0/8.
- Destination AS announces 1.0.0.0/8.
- A different AS announces a more specific 1.2.3.0/24.
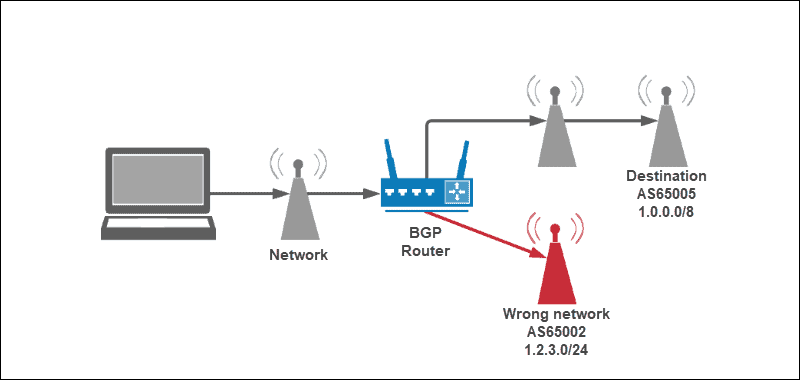
Since 1.2.3.0/24 is a better match, all data in the 1.2.3.0 range goes to the wrong network.
What is RPKI?
RPKI (Resource Public Key Infrastructure) is a security layer in BGP routing that provides full cryptographic trust towards ownership where the owners have a publicly available identifier. With BGP, the ground truth of ownership does not exist. Anyone is allowed to advertise a better route, whether maliciously or accidentally.
RPKI is based on the existing PKI standard – RFC6480. There are a lot of references to the existing cryptography methodologies for secure communication.
Why is RPKI Important?
Resource Public Key Infrastructure makes BGP more secure and reliable. The vulnerability of the Internet due to how BGP works is a systematic problem. With the growth of the Internet, the consequences are more noticeable.
Routing information to a small network creates an overload. Malicious routing brings sensitive information to the wrong place. BGP errors have the potential for fraud and large-scale outages. Some notable cases are:
- Amazon – Route 53 BGP hijack of Amazon DNS for a cryptocurrency heist.
- Google – Misconfiguration of BGP filtering during an update routed traffic to China, Russia, and Nigeria.
- Mastercard, Visa, and major banks – Leaked 36 prefixes of payment services.
- YouTube – An attempt to block the YouTube website in Pakistan ended up taking it down.
What Form of Protection Does RPKI Offer?
BGP problems arise for numerous reasons:
- No reliable security plan
- Redistribution mistakes
- Typos
- Malice
The most common factor is human error.
The cryptography model of RPKI provides ownership authentication through a public key and certificate infrastructure without having identifying information in them. The certificates add a layer of network security to the IPv4 and IPv6 prefixes. The RPKI certificates are renewed every year. HTTP uses similar encryption to secure web pages.
Although the whole path is not secured, RPKI verifies the identity of the origin and provides a way to confirm that they are who they say they are. RPKI is a step in securing BGP routing where we know the origin of the incoming information and who owns which space.
Widespread deployment makes it even more efficient in preventing hijacks overall.
RPKI Benefits
Implementing and using RPKI comes with the following benefits:
- Proof of origin. Resource holders have ownership proof to use specific resources through a signed certificate trust chain, helping prevent mistakes about the information origin.
- Cryptographic identity verification. Resource holders have a way to prove ownership to customers when distributing resources.
- Route hijacking prevention. Resource users protect the information provided by resource holders through a digital signature, which a verified resource holder generates and supplies to the user. Attempts to alter the signature renders it invalid.
How Does RPKI Work?
The RIR (Regional Internet Registry) provides the root trust of the RPKI cryptography model. The IANA (Internet Assigned Numbers Authority) is a part of ICANN (Internet Corporation for Assigned Names and Numbers) who owns IPv4 and IPv6 address space.
IANA suballocates chunks of IP space to RIRs. The local RIRs then suballocate IP space to networks, which further suballocate to smaller networks. This path creates a trusted chain in signing certificates. The RIR regions divide into five geographic areas:
| Acronym | Full Name | Region |
| ARIN | American Registry for Internet Numbers | North America |
| LACNIC | Latin America and Caribbean Network Information Centre | Latin America |
| RIPE NCC | Réseaux IP Européens Network Coordination Centre | Europe, West Asia, and the former USSR |
| AFRINIC | African Network Information Centre | Africa |
| APNIC | Asia Pacific Network Information Centre | Asia Pacific |
ROA
The final part of the chain is the ROA (Route Origin Authorization). The ROA is a simple document with two pieces of information:
1. What the route is and the maximum length.
2. The AS announcing the route.
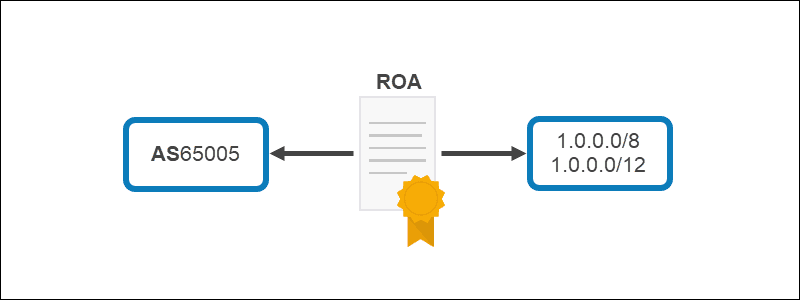
For example, if AS65005 announces in the range 1.0.0.0/8 to 1.0.0.0/12, the ROA contains the scope and the AS65005 identifier, validating who the real owner of the information is with complete trust.
How to Create an ROA
There are several things to consider before creating an ROA:
- Only prefix owners can create an ROA.
- Each ROA is specific to one of the existing RIRs.
- Owners need to generate an ROA request key pair prior to creating the ROA.
- ROA requests are submitted to the appropriate RIR.
For in-depth information on how to create an ROA, please refer to the instructions outlined by each respective RIR:
How is RPKI Deployed?
The P in RPKI means the certificates and ROAs are accessible in public repositories. The information is used to generate lists of which prefixes belong to which ASNs.
The signatures of the certificates and the lifetime of the ROAs get checked by each network independently. If any of the following fails, the ROA is ignored:
1. The start date or end date of ROA and the certificates chaining back to the root are in the past or future.
2. Any of the signatures are invalid or revoked.
All the ROAs which passed the test cache into a validated list. A filter is generated and uploaded to the routers based on the validated cache list. Routers check BGP advertisements through the filter with one of the three results:
- Valid – ROA is present. The prefix length and AS number match.
- Invalid – ROA is present. The prefix length or AS number does not match.
- Not-found or Unknown – No ROA present.
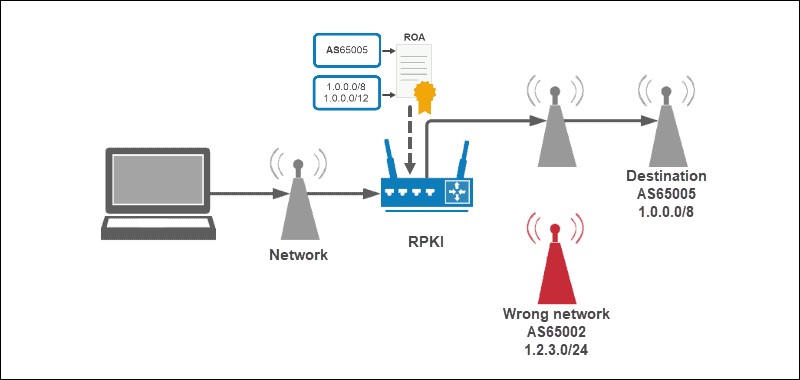
The router acts based on the state of the prefix generated by the filter.
Signing Prefixes
RIRs offer online tools for signing prefixes. This links a prefix and prefix length to an AS. Once a prefix is signed, others who have implemented RPKI validation can validate the prefixes.
Certificate signing prevents the prefixes from being hijacked (intentionally or unintentionally). Signed certificates are the core of ROA. RPKI offers no path validation and man-in-the-middle attacks are still possible.
Validating Prefixes
Implementing validation depends on network details. The general steps in setting up a network for prefix validation are:
1. Installing RPKI validators – Software that retrieves RPKI data from all Internet Routing Registries (IRRs) and verifies signatures.
2. Configure validation on border routers with the route validator – The routers fill the validation cache with combinations of validated prefixes, prefix lengths, and source ASNs.
3. Implementing BGP filters on external BGP sessions – Adding a policy to all BGP sessions (peer, transit, and customers) to reject any prefix that is RPKI Invalid.
Conclusion
RPKI provides a step in securing BGP routing. Most router software and environments have RPKI available.
Read our article on 19 Cybersecurity Best Practices to Protect Your Business for more cybersecurity information.