iptables is a Linux firewall utility that protects your local network from untrusted sources. This firewall is based on chains that use rules to restrict or allow traffic to the machine.
This tutorial will teach you how to list and delete iptables rules.
Prerequisites
- A Linux system (This tutorial uses Ubuntu 20.02).
- Access to the Terminal.
- Sudo privileges.
List iptables Rules
The sections below show how to list rules by specifications or in a table. The output is the same, but the data is formatted differently. Moreover, the results can also be filtered to show rules for specific chains only.
List iptables Rules Based on Specifications
The standard command to list rules based on specifications is:
sudo iptables -S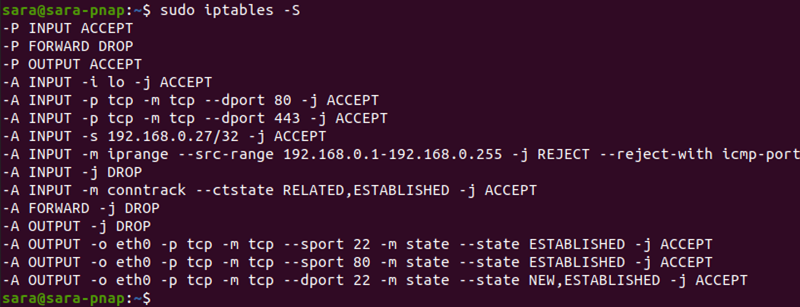
The output print rules as a list of specifications. However, to list only rules for a specific chain, include the chain's name:
sudo iptables -S OUTPUT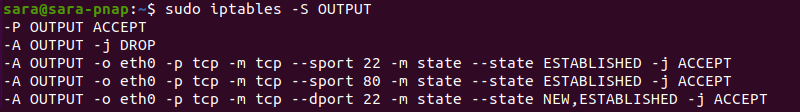
List Rules as a Table
To list all the iptables rules in a table, sorted by chains, use:
sudo iptables -L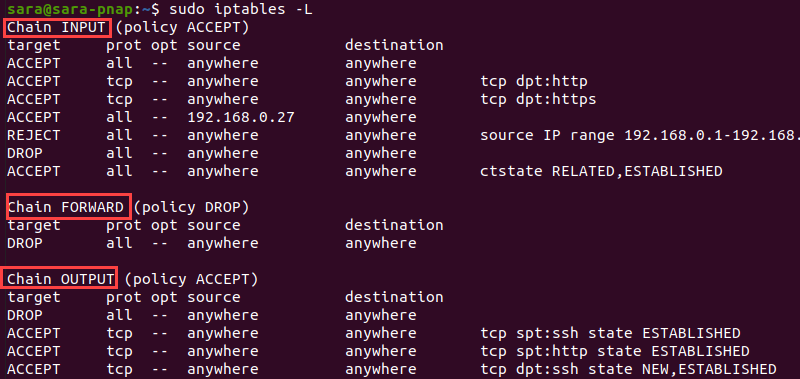
The output shows rules sorted by three chains: INPUT, FORWARD, and OUTPUT. Use the chain name with the command to print the details for that chain:
sudo iptables -L INPUT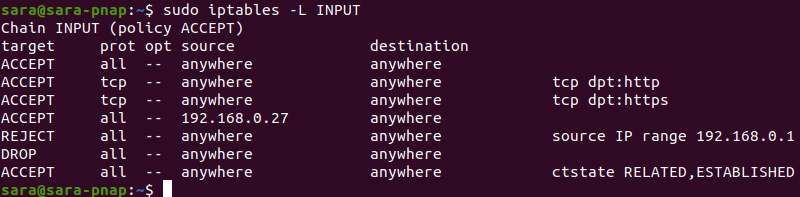
List Packet Counts
Listing rules in a table or by specifications displays chain name, default policy, target, protocol, IP option, and source and destination IP addresses.
However, the -L and -v arguments print additional info, like the number of packets that match every rule and the total packet size.
To accomplish this, execute:
sudo iptables -L -v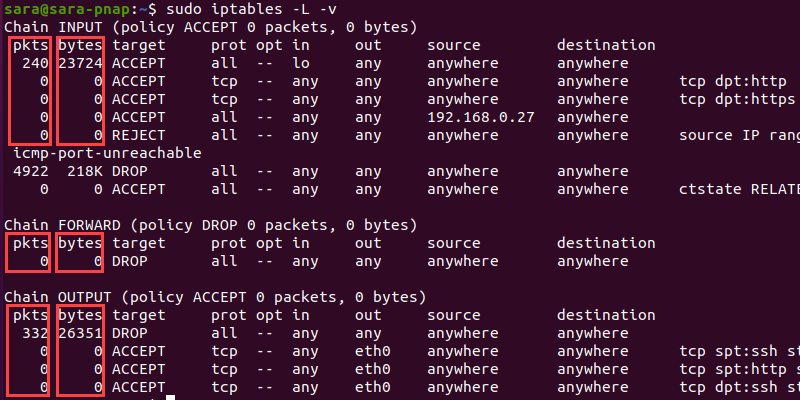
The command prints two more columns, bytes and pkts. The -L and -v arguments also work when applied on a single chain. For instance:
sudo iptables -L INPUT -v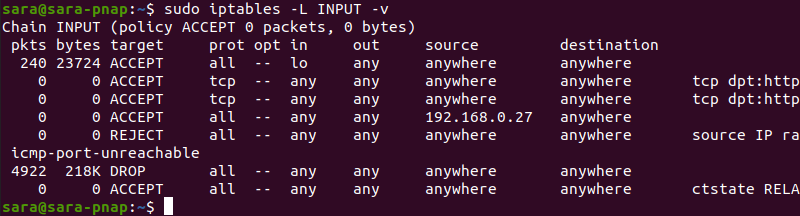
Reset Packet Counts
The simplest way to reset iptables byte counters is to reboot the system. Another option is the -Z argument:
sudo iptables -Z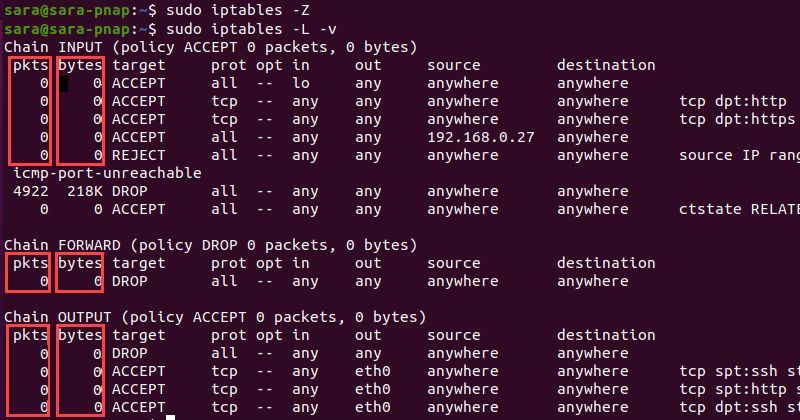
This command clears the counters in all chains.
Delete iptables Rules
The -D argument used with iptables deletes a specific rule. The -F option removes all rules in the chain. Use one of the methods to delete rules based on specifications, chains, or numbers, or to flush the entire chain.
Delete iptables Rules by Specifications
Use -D with a rule specification to remove that specific rule. To make the process more straightforward, run the command with the -S argument first.
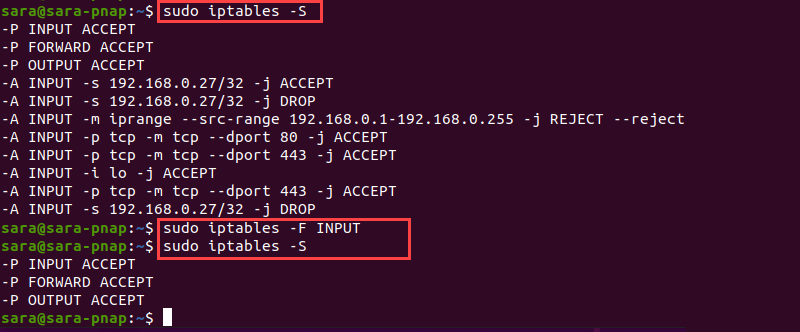
sudo iptables -S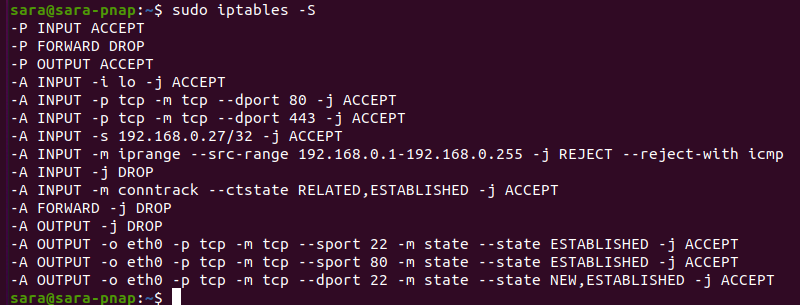
The output lists all iptables rules and specifications. Choose a rule to delete and copy/paste the specification into the following command:
sudo iptables -D [specification]Warning: When copying the specification, omit the -A option.
For example, to delete the -A INPUT -j DROP rule from the list, execute:
sudo iptables -D INPUT -j DROPThe command prints no output, but to verify the result, run sudo iptables -S again:
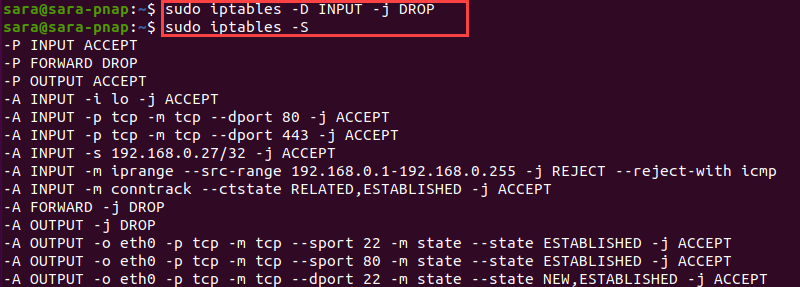
The output shows that the -A INPUT -j DROP rule and specifications are not on the list anymore.
Delete Rules by Chains and Numbers
A more straightforward way to delete rules is to use line numbers for chains. First, list iptables rules as a table, but add the --line-numbers argument:
sudo iptables -L --line-numbers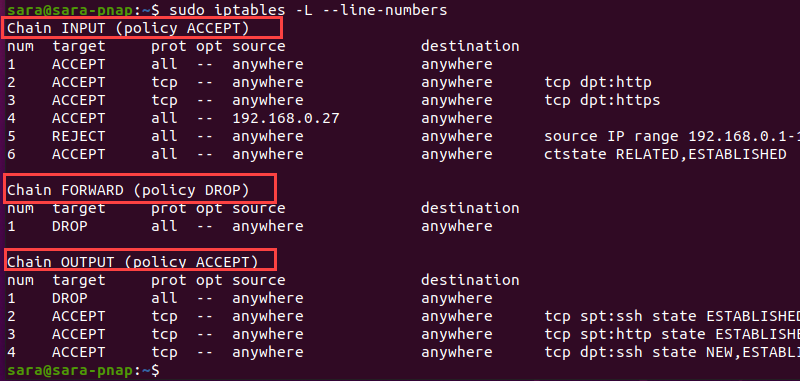
The output also shows three chains: INPUT, FORWARD, and OUTPUT, and adds line numbers for every rule listed under each chain.
To delete a specific rule, include the chain name and the line number:
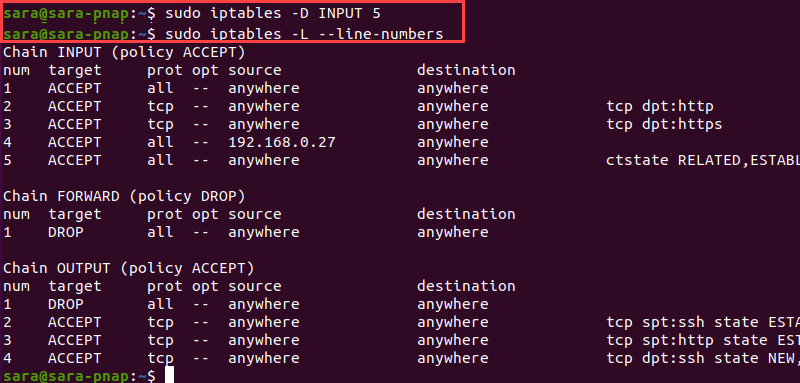
sudo iptables -D [CHAIN] [LINE_NUMBER]For instance, to delete a rule with line number 5 from the INPUT chain, execute:
sudo iptables -D INPUT 5The -D option doesn't show any output, but iptables -L verifies the outcome:
Delete All Rules in a Chain (Flush Chain)
Flush a chain with -F to remove all rules and delete that chain. Moreover, the -F argument deletes multiple chains.
To flush a single chain, use -F with the chain name. For instance, the OUTPUT chain has four rules:
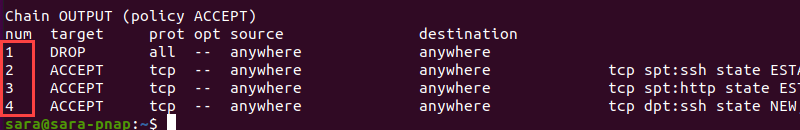
Flush the entire OUTPUT chain and delete both iptables rules with the following:
sudo iptables -F OUTPUTThe command doesn’t print any output. Therefore, verify the outcome with:
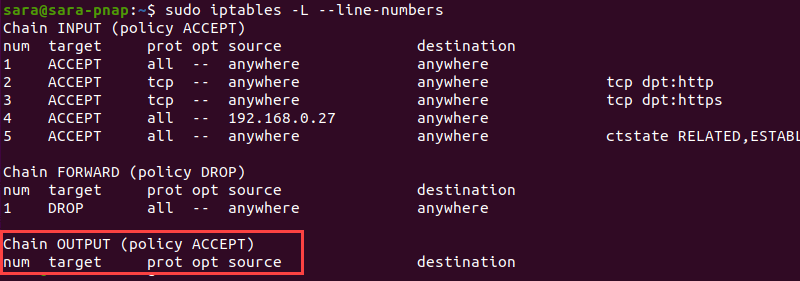
Flush All Chains
Flushing all chains removes all iptables rules and disables the firewall. Follow this process only when starting or restarting the firewall configuration.
Take the following steps:
1. Change the default policy for every built-in chain to ACCEPT to avoid getting shut out via SSH with:
sudo iptables -P INPUT ACCEPTsudo iptables -P FORWARD ACCEPTsudo iptables -P OUTPUT ACCEPT2. Flush all mangle tables and net tables with:
sudo iptables -t mangle -Fsudo iptables -t nat -F3. Remove all non-default chains:
sudo iptables -X4. Flush all chains with:
sudo iptables -FNote that none of these commands prints any output. To verify that all chains are flushed, run sudo iptables -L --line-numbers again:
Conclusion
After this tutorial, you know how to list and delete iptables rules. Next, read this complete iptables tutorial for even more info.