Social media is one of the most powerful tools for boosting visibility and engaging a wider audience. However, mismanaged social media accounts are open doors for hackers, disgruntled employees, and malicious competitors who want to tarnish your brand image. Although generally secure, social media platforms bypass your established cybersecurity safeguards and open new avenues for security breaches.
To avoid this issue, you must integrate social media into your cybersecurity strategy and treat social accounts as vulnerable points within your IT infrastructure.
This article outlines social media security best practices that will keep your brand's voice secure and trustworthy across all digital channels.

What Is Social Media Security?
Social media security is a set of strategies and tactics that protect the privacy and security of your company and customers from cyber attacks on social media platforms.
Why Is Social Media Security Important?
If hackers take control of your organization’s account, the potential consequences are dire:
- Compromised data. Hackers will exploit any data they can get their hands on. The names, birthdays, private messages, and even financial details of your customers or employees could be sold on the dark web or used to launch further attacks on your network.
- Tarnished reputation. Hackers can masquerade as your company and spread misleading information that could damage your brand image and erode public trust.
- Phishing attacks. By impersonating your company, hackers can launch effective spear phishing campaigns, tricking your customers or employees into clicking on malicious links that contain malware.
- Permanent account loss. In the worst case, hackers could permanently steal your company's account, potentially even renaming or shutting it down entirely.
Here are some notable examples of cyber attacks that targeted the social media accounts of renowned organizations.
Mandiant Hack
In January 2024, hackers took over the X account of Mandiant, an American cybersecurity firm and Google subsidiary. They renamed the account and promoted a fake website posing as a crypto wallet. The fake site promised free crypto tokens but drained the victim's cryptocurrency wallets through a phishing attack.
Mandiant has since regained control of its account, but at the time of writing this article, the username '@phantomsolw' remains due to X's restrictions on frequent name changes.
Burger King Hack
In 2013, the hacker group Anonymous hijacked Burger King's Twitter account. As part of an elaborate prank, the hackers replaced Burger King's profile picture with a McDonald's logo and renamed the account. They also announced that Burger King was being sold to McDonald's and posted tweets using inappropriate language, racial slurs, and drug references.
After an hour, Twitter suspended the account. Shortly after, Burger King regained control and apologized for the incident.
Associated Press (AP) Hack
In 2013, hackers associated with the Syrian Electronic Army (SEA) hijacked the Associated Press (AP) Twitter account. They sent out a false tweet claiming that there had been two explosions at the White House and that President Barack Obama was injured.
The fake tweet caused widespread panic and confusion, briefly sending the Dow Jones Industrial Average down by 150 points. The AP quickly issued a correction, but the damage was done.
The hackers accessed the AP's Twitter account through phishing emails sent to AP employees.

Social Media Security Risks and Threats
Social media platforms have robust cybersecurity. They possess layers of expert-built security tools, 24/7 cloud monitoring, and servers in physically secure hyperscale data centers.
However, determined attackers employ social engineering tactics to target the weakest link. A hacker might impersonate a social media manager's friend or coworker to trick them into revealing sensitive information or granting access to an account. Alternatively, they might frighten the social media manager into clicking on a phishing link by claiming an urgent issue.
Here is a consolidated overview of prevalent social media security risks and threats.
Phishing
Phishing involves hackers crafting messages, posts, or pages that deceive social media managers into clicking on malicious links. Embedded within these links are attachments that, when opened, infect the victim's device and potentially spread to the organization's network via lateral movement.
Another common variation of social media phishing is lookalike login pages. Hackers create fake websites that closely resemble the real login pages of popular social media platforms. These pages trick users into entering their login credentials on the fake page, which the attackers can then steal and use to access the victim's accounts.
Spear Phishing
Spear phishing leverages personalization to target individuals or groups within an organization. Hackers comb social media, collecting personal details, interests, and professional information about their targets. Armed with this intel, they craft highly persuasive messages that mention familiar names, relevant contexts, and internal jargon. This additional measure significantly increases the probability of the target falling victim to the phishing attack.
An example of this kind of attack would be a social media manager who receives a direct message on LinkedIn from a supposed recruiter at their dream company. The message references a recent project the manager showcased on their profile, mentioning specific skills and experience. It even includes a link to a "confidential job application" hosted on a website that appears genuine. Excited by the prospect, the manager clicks the link and falls victim to a spear phishing attack.
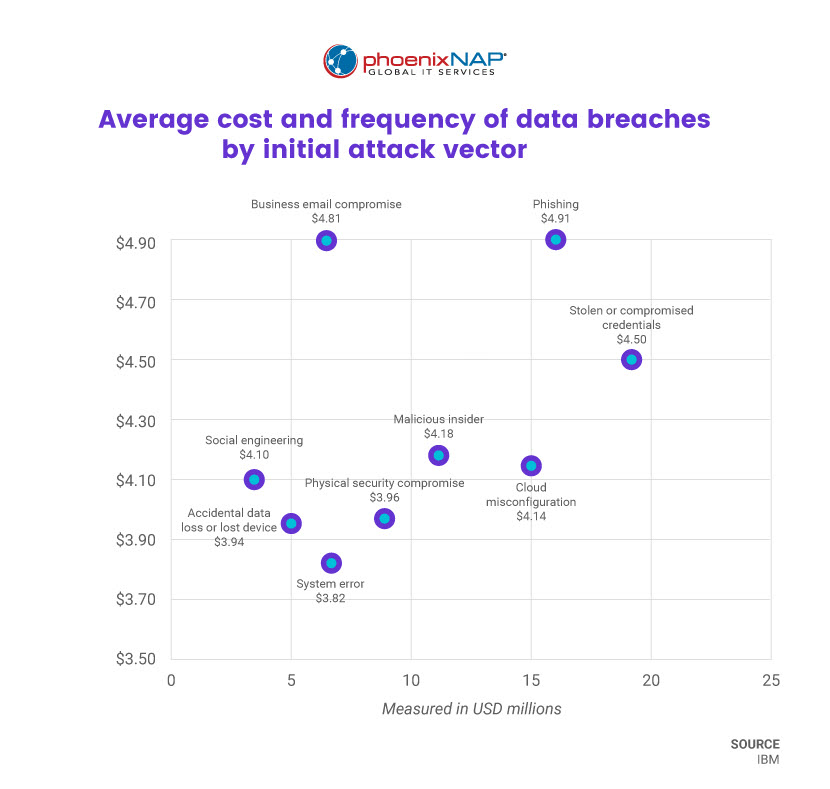
Data Breaches
Social media presents a unique challenge for data security. Employees with privileged access to social media accounts may publicly share confidential information due to social engineering, oversight, or improper data handling procedures.
Furthermore, a disgruntled social media manager is one of the most dangerous forms of insider threat. Driven by malice or a desire for personal gain, they may deliberately leak customer data, post damaging information about the company, or expose internal processes and marketing strategies.
Credential Stuffing
This tactic exploits the all-too-common tendency to reuse login credentials across platforms. Hackers purchase massive databases of breached usernames and passwords from illegal online markets, then unleash automated attacks using specialized tools.
These tools bombard websites with thousands of login attempts simultaneously, attempting to unlock accounts on various platforms with a single stolen key. If your organization has reused the same or similar login credentials on multiple platforms, a breach on one is likely a breach on all.
Malicious Browser Extensions
Malicious browser extensions steal your organization's data, hijack your accounts, and spread harmful content without your knowledge.
In a recent example, a Chrome extension called Quick Access to ChatGPT compromised thousands of Facebook business accounts. Disguised as a convenient tool for interacting with ChatGPT, the extension secretly collected user information, stole browser cookies, and installed a backdoor that granted the malware author super-admin permissions to the victim's Facebook account.
Software Vulnerabilities
Failing to update social media management software and device operating systems exposes them to known vulnerabilities. Hackers constantly seek and exploit such vulnerabilities to infiltrate systems and access sensitive information.
Furthermore, connecting third-party apps to social media accounts grants them access to your account's data. If these apps have security flaws, hackers can exploit them to access your accounts.
Social Media Security: 6 Best Practices
Social media security is more than damage control – it is preemptive risk management.
Here are six best practices for safeguarding your online presence.
1. Lock Down Accounts
- Use strong passwords. Enforce a strong password policy that requires employees to use unique, complex passwords for each social media account. The passwords must not contain common phrases, birthdays, or dictionary words. Consider using a password manager to generate and store strong passwords securely.
- Avoid recycled passwords. Use a unique password for each account to minimize the risk of other accounts being compromised in case of a data breach or a credential-stuffing attack.
- Enable two-factor authentication (2FA). 2FA adds an extra layer of security by requiring a second verification code, usually sent to your phone or email, in addition to a password.
- Implement role-based access control. Limit access to accounts and passwords based on roles and responsibilities. Not everyone involved in social media management requires posting or admin privileges. Regularly review and update account permissions and revoke access for former personnel.
2. Educate Your Employees
- Organize security awareness training. Regularly conduct security awareness training for employees who manage social media accounts. Educate them on common phishing and social engineering tactics, as well as cybersecurity best practices.
- Establish clear ownership. Set up a transparent hierarchy of team members responsible for each social media account, with clearly defined roles and access levels.
- Set clear guidelines. Establish clear social media protocols for acceptable use and content sharing. The guidelines should limit personal social media use on business devices and restrict risky behavior, such as engaging in online quizzes that request personal information.
- Promote open communication. Encourage your staff to report on suspicious activity and security concerns.
3. Secure Your Devices
- Regularly update software. Keep all software and devices used for social media management up to date with the latest patches.
- Maintain network security. Use firewalls, intrusion detection systems, and virtual private networks (VPNs) to protect your systems from unauthorized access.
- Avoid public Wi-Fi. Ensure that your employees avoid using public Wi-Fi for work. Hackers can exploit weak security protocols on public networks to intercept traffic and access sensitive information.
- Strengthen endpoint protection. Install and maintain endpoint security software on all devices used for social media management. Endpoint security software includes features like antivirus, anti-malware, and phishing protection.
4. Manage Third-Party Tools with Care
- Conduct thorough research. Carefully research and evaluate any third-party social media management tools before integrating them with your accounts. Ensure they have robust security and a good reputation.
- Limit access. Grant only the minimum level of access required for each third-party tool and revoke access when no longer needed.
- Ensure data security and compliance. Understand the data security practices of the third-party tools you use and ensure they comply with relevant data privacy regulations like HIPAA, GDPR, and PCI.
5. Stay Vigilant
- Perform regular monitoring. Regularly inspect your social media accounts for suspicious activity, such as unauthorized login attempts, unusual posts, or changes to account settings.
- Watch out for brand impersonation. Stay alert for imitations of your account and report them to platform administrators and your followers.
- Know the threats. Stay informed about security-related news specific to different platforms. When you learn about new vulnerabilities or hacking incidents, quickly address similar issues within your accounts to mitigate risks.
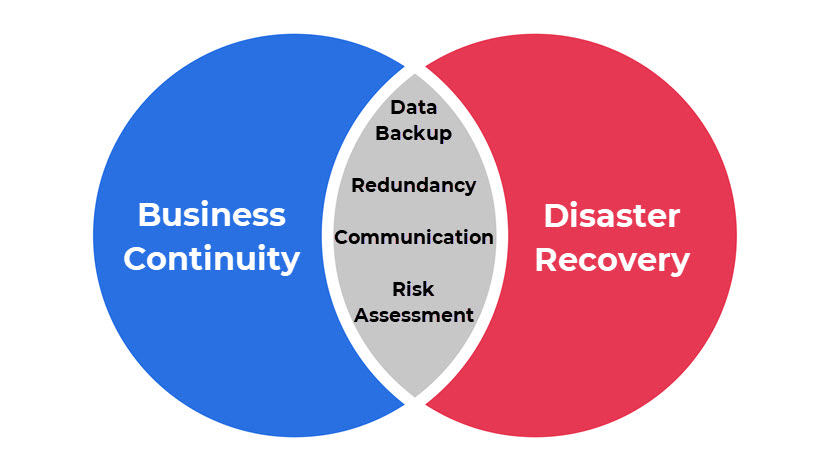
6. Plan for Disaster
- Have a comprehensive crisis management, incident response, and disaster recovery plan. These policies outline how you'll address security breaches, minimize damage, and quickly restore business continuity.
- Have a backup strategy for your social media data. Having readily accessible backup servers ensures quick recovery in case of account compromise or data loss.
Building Resilience for Your Social Media Presence
While implementing these best practices bolsters your defense, even the most secure systems are not invincible. In recent years, we have witnessed major hacks on almost all social media platforms. In 2022, a Facebook API vulnerability exposed over 533 million profiles, and a 2021 LinkedIn breach leaked information on 700 million users.
As consumers of social media, we can do little to prevent these attacks. However, we can mitigate their impact on our business. By adopting the core practices outlined in this article, you will be well-equipped to maintain social media security, even in the face of unforeseen platform-wide attacks.



