Modern data centers use physical servers with hypervisors to run virtual machines. This way, virtualization brought cost-effectiveness and enhanced scalability. With virtualized network solutions, such as VMware's NSX software, the concept of networking acquired a new meaning.
The software-defined networking model, or SDN, provides all the necessary features to create complex network configurations. SDN provides high security and enables seamless scaling without extensive physical network changes due to its agile and flexible nature.
This article examines what VMware NSX is and the differences between VMware NSX-V and VMware NSX-T.

VMware NSX
In the virtualization market space, VMware is one of the biggest names. The company offers an array of products for virtual workstations, network virtualization, and security platforms.
VMware NSX is an advanced SDN solution with two variants:
- NSX-V
- NSX-T
What Is VMware NSX?
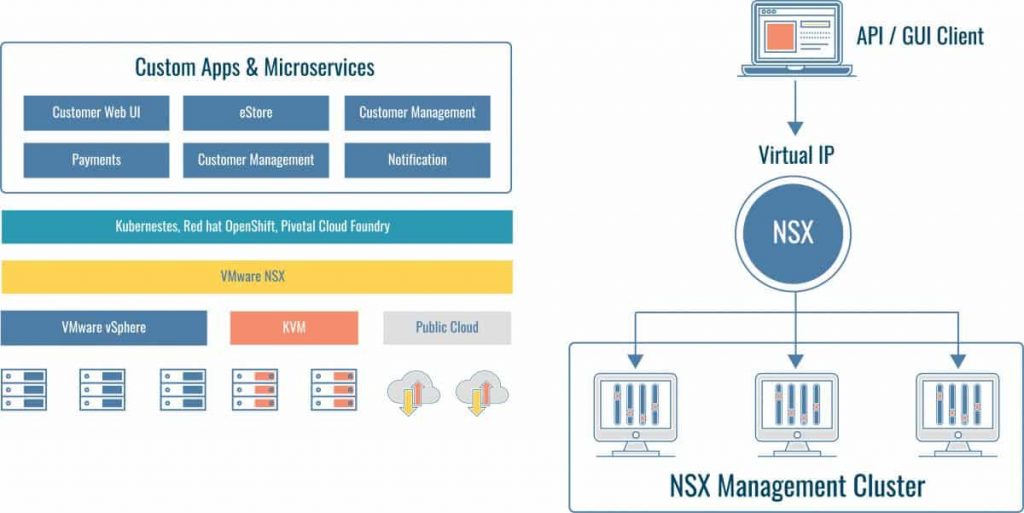
NSX is a software-defined networking solution that VMware created to tackle the rapid growth of data center networking needs. The main function is to provide virtualized network creation and management via NSX Manager, a component of NSX Data Center. Additionally, VMware NSX provides crucial network security features to ensure the virtual environment is safe.
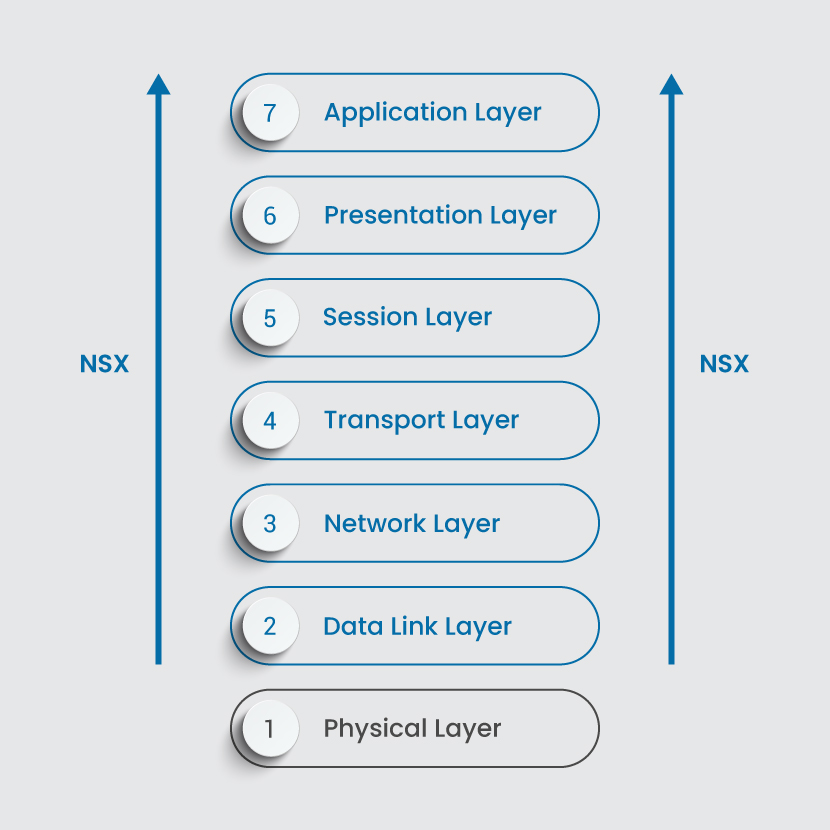
With NSX, no changes to the underlying hardware are necessary. Network provisioning and connection between virtual networks are abstracted from the hardware, similar to how VMs work. NSX virtualizes switches, routers, firewalls, and other network services from Layer 2 to Layer 7 of the OSI model.
This process saves time, effort, and costs, enabling large companies to centralize and automate network management and control. Depending on the product you choose, VMware NSX is suitable for all infrastructure types:
- Multi-cloud environments
- On-premises data centers
- Bare metal servers
- Containerized workloads
Read on below to learn the differences between NSX-V and NSX-T.
What Is NSX-V?
NSX-V architecture (V as in vSphere) features deployment reconfiguration, rapid provisioning, and destruction of on-demand virtual networks. This product depends on VMware vSphere and a connection with vCenter. Once NSX-V pairs with vCenter, the integration with vSphere is seamless.
The downside is that you cannot have multiple vCenters with NSX-V. The question arises: what if I have more than one vCenter? In that case, you must have multiple NSX managers, which can be challenging in multi-cloud environments. The maintenance can become cumbersome and demanding. As companies transition to the cloud for handling workloads, the VMware NSX-V solution proves unsuitable for many clients. Now more of a legacy VMware product, NSX-V is being replaced by NSX-T.
What Is NSX-T?
VMware NSX-Transformers is a successor to NSX-V and offers options to build a highly agile SDN infrastructure. The product brings network virtualization to bare-metal and containerized workloads, multi-cloud, and multi-hypervisor environments. NSX-T supports cloud-native applications, a network virtualization stack for OpenStack, Kubernetes, KVM, Docker, etc.
Many consider NSX-T as an upgrade of NSX-V. The main idea behind both products is indeed the same. However, VMware built NSX-T from the ground up, and what lies under the hood differs completely from NSX-V.
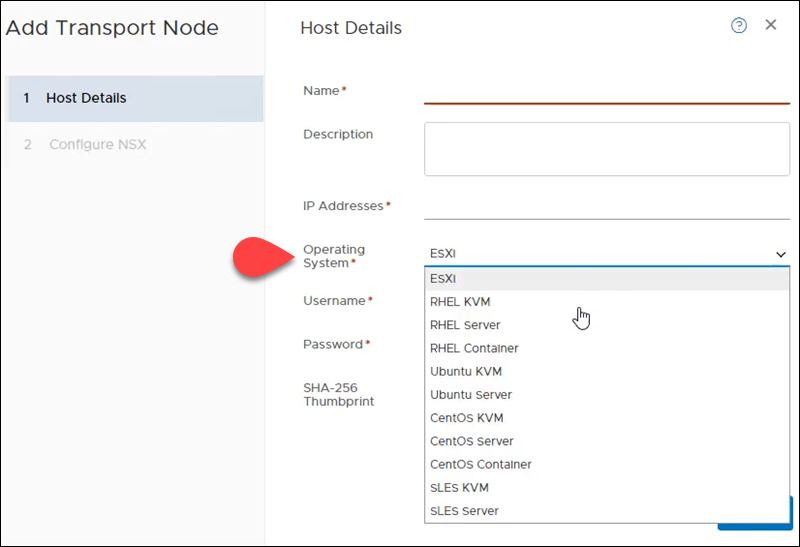
The main benefit is that NSX-T can be deployed in heterogeneous environments with many different components. NSX-T is not under the confines of the vCenter deployment. You can have multiple vCenter servers and use one NSX manager as a single pane of glass for controlling your virtual network. Or, you do not have to deploy a vCenter at all. Instead, you can choose ESXi as the operating system in the NSX-T GUI, for example.
NSX-V vs. NSX-T Interface
There is no dedicated NSX-V interface labeled by that name. With NSX-V installation comes a plugin that integrates into vCenter Server. Therefore, to access the GUI options for NSX-V, you log in to your vSphere instance and select the Networking and Security option.
For example, this is the section in the vSphere Web Client for NSX-V:
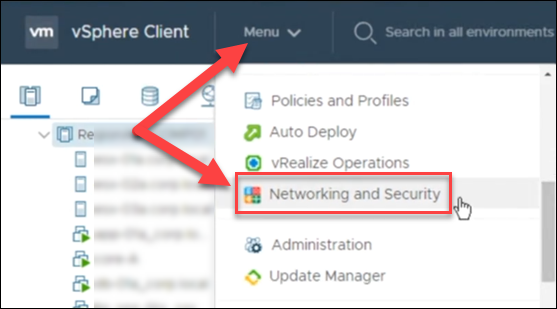
If this option does not appear in your GUI, then the account you use does not have the necessary permissions. Only the user who connected NSX Manager to vCenter Server gets the Enterprise Administrator access. All other accounts have service rights only and need to be assigned proper permissions.
NSX-T has its own interface, decoupled from vCenter, called NSX-T Manager. This means you do not have to log in to vCenter to manage your NSX-T architecture.
When you log in to the NSX-T manager, the home page shows the networking, security, system, and inventory overview, alarms, etc.
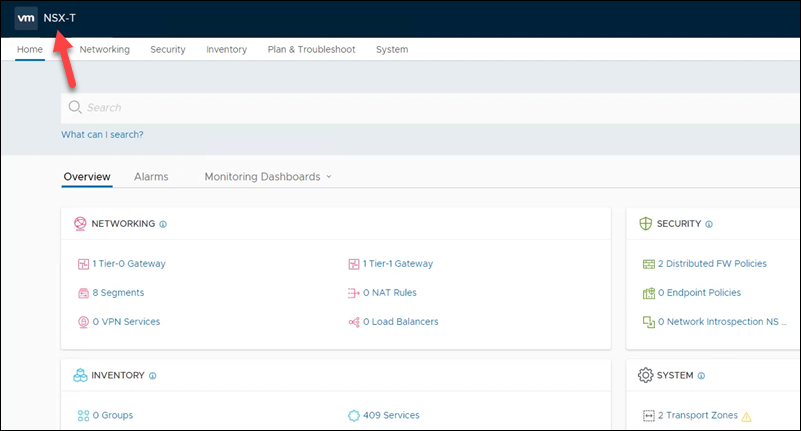
From the NSX-T Manager Web Client, you can view your vCenters or add new ones to pull inventory. This is where NSX-T outshines NSX-V with the ability to manage network and security automation across multiple vCenters.
NSX Main Components
The primary components of VMware NSX are:
- NSX Manager
- NSX Controller
- NSX Edge
NSX Manager
NSX Manager is the primary component used to configure, manage, and monitor all NSX components via a GUI. With the REST APIs, the configuration and object manipulation are consistent.
NSX-V APIs and NSX-T APIs are not the same.
NSX Manager lets you deploy controllers, edge distributed routers, and generate certificates. In NSX-V, the NSX Manager works with one vCenter Server as a single virtual machine. In the case of NSX-T, the NSX-T Manager can be connected to multiple vCenters as a KVM or ESXi VM, for example.
NSX Edge
VMware NSX Edge Services Gateway (ESG) is a part of VMware vCenter Server and provides essential gateway services such as:
- DHCP
- NAT
- VPN
- Load balancing
- Perimeter firewall
- Dynamic routing
NSX Edge enables the connection between isolated and shared networks and direct connection between VMs. Besides the east-west routing, this service allows tenants to reach public networks by providing the north-south connection. Using NSX Edge lets you create virtual boundaries for your workloads, components, and tenants.
NSX Controllers
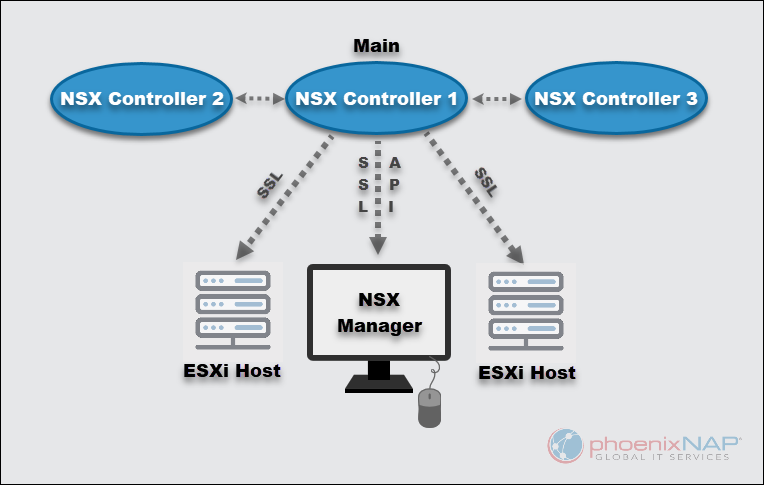
NSX Controller is a distributed state management system and the central control spot for logical switching and routing. The controllers contain all information about hosts, VMs, distributed logical routers, and VXLANs.
This virtual appliance is crucial for installing and monitoring scalable and highly available virtual networks. No matter the size of a software-defined data center, VMware requires exactly three controllers in NSX-T to achieve the necessary redundancy.
NSX Controller uses a Secure Sockets Layer connection to connect to ESXi hosts and the SSL API to interact with NSX Manager.
Features of NSX
Both NSX-V and NSX-T have the same goal in mind: to provide features to deploy virtual networks on top of the physical network.
Some of the NSX features include:
- Distributed logical routing, switching, and other features listed in the NSX Edge section above.
- Detailed monitoring and statistics
- Quality of Service (QoS)
- API-driven automation
- Software-based overlay
- Enhanced user interface
The available features depend on the NSX license you purchase.
However, the two tools have many differences, and they are built as two different products. NSX-V cannot work with multiple vCenters and strongly depends on vSphere.
On the other hand, NSX-T is a cross-platform solution that works with multiple vCenter instances and different environments. The latest NSX-T features also include NSX-V to NSX-T Migration and distributed IDS/IPS.
Explore the comparison table below and the sections for feature details to understand the differences between NSX-V and NSX-T better.
VMware NSX-V vs. NSX-T Comparison
| Comparison of Features | NSX-V | NSX-T |
|---|---|---|
| Basic Functions | NSX-V offers rich features such as deployment reconfiguration, rapid provisioning, and destruction of any on-demand virtual network. This allows a single virtual switch to connect to multiple hosts in a cluster by utilizing the vSphere distributed switch. | NSX-T provides users with an agile software-defined infrastructure. It is suitable for building cloud-native application environments. It also provides simplicity for operations in networking and security. Has built-in support for multiple clouds, multi-hypervisor environments, and bare-metal workloads. |
| Origins | Initially released in 2012, NSX-V is built around the VMware vSphere environment. | NSX-T originates from the vSphere ecosystem, but it is built from scratch and designed to address some of the use cases not covered by NSX-V. |
| Coverage | NSX-V architecture was built with on-premises (physical network) vSphere deployments in mind and one vCenter Server. | NSX-T extends its coverage to include multiple hypervisors, containers, cloud environments, and bare metal servers. NSX-T has some limitations with gaps concerning micro-segmentation. |
| Hypervisor Support | vSphere network virtualization stack is supported. | In addition to the vSphere stack, NSX-T also supports OpenStack, Docker, KVM, Kubernetes, etc. |
| Migration | NSX-T to NSX-V migration is not possible. | NSX-T Manager has a migration utility built in for users who want to migrate from NSX-V to NSX-T. |
| Working with NSX Manager | NSX-V Manager works with only one vCenter Server. Runs on Photon OS. | NSX-T Manager supports working with multiple vCenters at once. Runs on the Ubuntu operating system. |
| Deployment | Can be deployed only as an ESXi VM. | NSX-T Manager acts as a standalone solution and can be deployed as an ESXi or KVM VM. |
| Routing | NSX-V uses network edge security and gateway services, which are used to isolate virtualized networks. NSX Edge is installed both as a logical distributed router and as an edge services gateway. | NSX-T routing is designed for cloud environments and multi-cloud use. It is designed for multi-tenancy use cases and is for heterogeneous environments. |
| Overlay Encapsulation Protocols | NSX-V uses the VXLAN encapsulation protocol | NSX-T uses Geneve, a more advanced protocol |
| Logical Switch Replication Modes | Unicast, Multicast, Hybrid | Unicast (Two-tier or Head) |
| Virtual Switches Usage | vSphere Distributed Switch (VDS) | Open vSwitch (OVS) or N-VDS |
| Two-tier Distributed Routing | Not Available | Available |
| APR Suppression | Available | Available |
| Integration for Traffic Inspection | Available | Not Available |
| Configuring IP Address Scheme for Network Segments | Manual | Automatic |
| Kernel-Level Distributed Firewall | Available | Available |
The table showed an NSX-V vs. NSX-T feature comparison summary. Read on to learn more details on the differences between the two solutions.
Routing
Both VMware NSX solutions provide dynamic routing capabilities that surpass those that physical routers offer. However, routing differences between NSX-V and NSX-T are numerous.
At its basis, NSX-T is designed with cloud multi-tenancy in mind. As the provider and tenant router configuration requires isolation, multi-tier routing support was introduced with NSX-T:
- Tier 0 logical routing for the provider admin user.
- Tier 1 logical routing control for the tenant admin user.
NSX-V ESG (Edge Services Gateway) provides essential DHCP, NAT, VPN services, and DLR (distributed logical routers) to isolate virtual networks. This way, NSX enables communication between VMs with fewer network hops than with traditional routing. However, the lack of support for tiered routing and multi-tenancy leaves NSX-V behind NSX-T.
Logical Switching and Bridging in NSX
NSX-V and NSX-T use overlay networks to mimic the conventional VLANs and provide easier network manipulation through logical switching and bridging. The functionalities resemble those of a physical network.
With NSX-V, logical switches are coupled with VXLANs to encapsulate and direct VM traffic to the physical network. By allowing Layer 2 bridging between a physical VLAN and a logical switch, NSX-V expands the pool of features. This includes linking physical with virtual components when complete virtualization is not possible. NSX-V supports multiple Layer 2 bridges.
Similar to its older counterpart, NSX-T provides overlay functionality using logical switching but with a more advanced encapsulation protocol. L2 bridging in NSX-T requires a dedicated bridge node to be created. Whereas in NSX-V, bridging happens on the hypervisor kernel level where a controller VM resides.
Overlay Encapsulation in NSX: VXLAN vs. Geneve
As with other features, NSX-V relies on more traditional VXLAN encapsulation when compared to NSX-T. Virtual Extensible LAN allows for creating around 16 million virtual network segments, surpassing the limitations of VLAN and 4094 possible networks. This number helped large organizations segment virtual network in a more relaxed manner.
Geneve stands for Generic Network Virtualization Encapsulation and compiles the best from other encapsulation protocols, including VXLAN and STT. NSX-T relies on Geneve to deliver virtual network identifier information with high throughput power and lower resource usage. Geneve is a flexible protocol, which means it can include other metadata as networks evolve.
Security and Micro-Segmentation
Both NSX-V and NSX-T allow organizations to separate data centers into logical network security segments and achieve workload-level application protection. This way, you can granularly define network security policies. You can segment a VDC around vCenter objects and hosts, VM names or features, or by using IP addresses, ports, etc.
NSX solutions use a hypervisor-level distributed firewall to handle all network parameters and security policies. You can use AD users and groups to define rules where an AD Domain Controller (ADDC) is deployed.
However, NSX-T offers more security features and a more granular security rule application than NSX-V. Nevertheless, all NSX security functions are built for continuous automation to avoid the confines of manual configuration and maintenance.
Deployment Options
The deployment process is quite similar for both products, yet there are many differences between the NSX-V and NSX-T features. Here are some critical discrepancies in deployment:
- With NSX-V, there is tight integration with VMware vSphere and vCenter. An NSX Manager instance is deployed as an ESXi VM only and has to be registered with vCenter. On the other hand, you can deploy NSX-T on either a KVM or ESXi VM, while vCenter is not required. Additionally, multiple NSX Managers are supported.
- In contrast to NSX-T where the Manager and Controller are included in the same virtual component, you need to deploy an NSX controller for NSX-V Manager.
- NSX-T lets you deploy a cluster of three NSX controllers for increased redundancy.
- It is not possible to use standard virtual switches with NSX-V, as it requires you to deploy a vDS. NSX-T uses a new virtual switch technology, N-VDS or Open vSwitches (OVS) for KVM hosts.
NSX Licensing
The good side of NSX-V and NSX-T licensing is that VMware does not divide the products. If you already have an NSX-V license, you can start using NSX-T whenever you are ready.
The solution is now called VMware NSX Data Center and has the following editions:
- Standard
- Professional
- Advanced
- Enterprise Plus
With the increase in remote work, VMware also introduced the Remote Office Branch Office edition (ROBO).
Choosing Between NSX-V and NSX-T
The major differences in NSX-V vs. NSX-T systems are evident in the table and the sections above. The first is closely associated with the VMware vSphere ecosystem. The other is unrestricted, not tied to a specific platform or hypervisor.

To determine which NSX option is better for you, take into consideration the use case for each product.
VMware NSX-V and NSX-T have many distinct features, a totally different code base, and cater to different use cases.
Choosing NSX-V
This product is still a valid choice in the following NSX-V use cases:
- For on-premises workloads without multiple hypervisors.
- When your data center uses only VMware vSphere.
- If your IT environment uses more than one vCenter instance.
- If you do not need a highly redundant on-prem infrastructure with multiple NSX Managers.
Choosing NSX-T
VMware NSX-T, with many updates and enhancements, overtook NSX-V in almost all cases. NSX-T use cases cover the following:
| Security | Automation | Multi-Cloud Virtual Networking | Cloud-native app support |
|---|---|---|---|
| Critical application lockdown | Fast deployment of full-stack applications. | Support for multi-cloud environments | Advanced networking and security features for microservices and containerized applications. |
| Protection of individual workloads | Integration with other automation tools. | Cross-site network virtualization for rapidly growing businesses. | Per-container security policies |
| Logical DMZ creation | Automatic security policy and access rule application when migrating VMs to other subnets. | Single to multi data center extension. | Native container-to-container Layer 3 networking |
| Micro-segmentation for granular security policies | Consistent and error-free network configuration and management |
Conclusion: VMware NSX Provides a Strong Network Virtualization Platform
NSX-V and NSX-T are advanced security virtualization platforms that simplify network management. As cloud environments grow, NSX-T - with its multi-site and cloud support- has become the preferred choice, now part of VMware NSX Data Center. Contact us to learn more about NSX solutions and NSX-V to NSX-T migration.